May 30, 2023 Shan
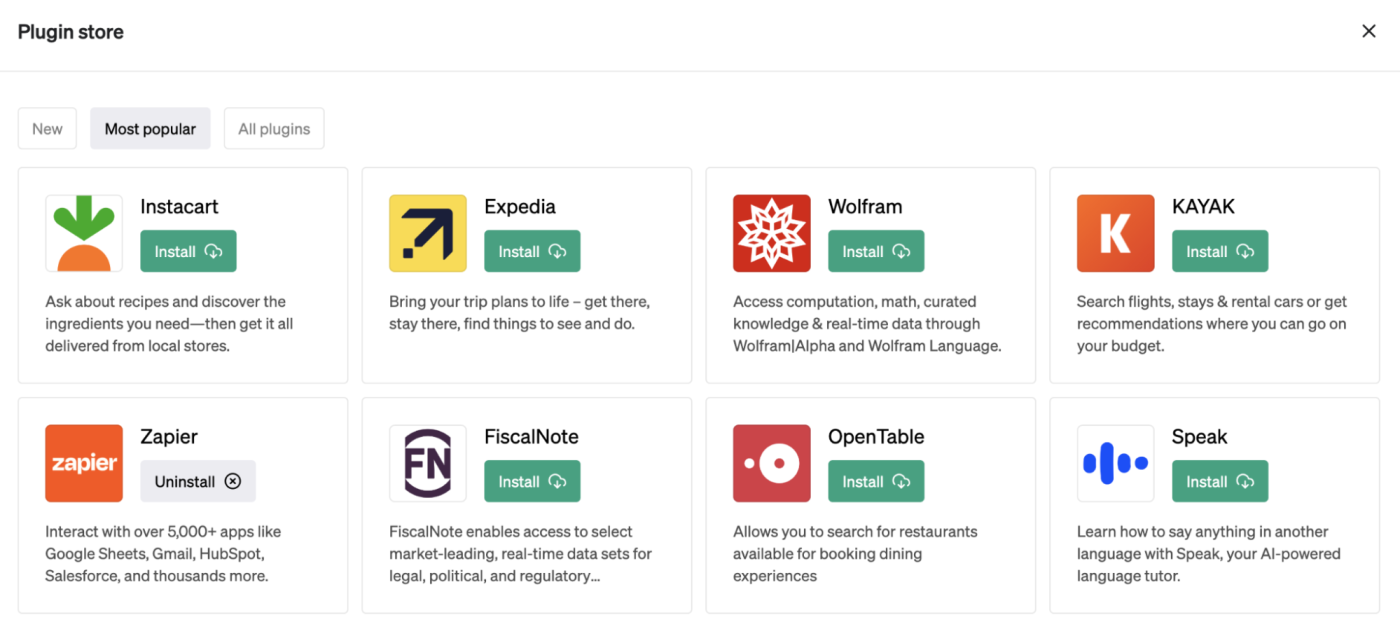
Unmanaged devices, external file-sharing, and email integration impose a big question mark on the security posture of Microsoft Teams. In order to secure and manage Microsoft Teams, policies are used under various sections like messaging, meetings, calling, conferencing, and many more. Usually, these Teams policies for users, groups, and batches are managed in the Microsoft Teams admin center or using the Teams PowerShell Module (TPM). But now Microsoft extends the managing capability of additional Office 365 group policies using the Teams PowerShell Module as per MC557818.
According to this latest update, group policy assignments for Microsoft 365 groups, distribution lists, mail-enabled security groups, and security groups support additional policies in the Teams PowerShell Module. Apart from action control, policy assignments also set way for security controls like restricting anonymous access in meetings.
Let us see how to assign group policies using Microsoft Teams PowerShell Module and their functionalities under this blog.
What are Group Policy Assignments?
As the name suggests, assigning a policy to a particular group of users is known as a group policy assignment. The groups can be managed in Microsoft 365 admin center whereas group policies can be managed under the single roof of the Teams PowerShell Module.
Policy assignments are applied only to the direct members of a group and not to the nested group. That too, they are applied according to the precedence rules. And at the time of addition or deletion of users from a group, the policy assignments are updated which is also applicable when a policy is unassigned. Before jumping into group policy assignments, let us look through the precedence rules and ranking of policies.
What are Microsoft Teams Policy Precedence Rules?
Policy precedence determines the user’s effective policy when a user is assigned two or more of the same policy types. The precedence rules of policies are listed below for deeper insights into how an assigned policy will be deployed according to these rules.
- If a user is directly assigned a policy, the same type of policy can’t be inherited from the group. Therefore, the directly assigned policy takes precedence over the same policy type defined by the group.
- Also, if a user doesn’t contain a directly assigned policy, the user inherits the highest-ranking policy from the same type of policies applied by two or more groups.
- Finally, if the user is not assigned a policy directly or by group, then the global (organization-wide) policy takes precedence.
The user policy is updated under the following circumstances.
- Especially when a user is added or removed from the policy assigned group.
- And when a group policy is unassigned.
- At last, if a directly assigned policy is removed from a user.
What is Group Policy Assignment Rank in Teams?
As an admin, you are asked to define the rank of policy while assigning the policy. Primarily this ranking weighs the priority of the same type of policies assigned from two or more groups for a common user. Finally, the highest-ranking group policy is assigned as the effective policy to the end user after weighing the priority. Because a policy type can be assigned to a maximum number of 64 groups in Office 365.
NOTE: If the rank value is undefined, then the lowest ranking is given to the policy assignment.
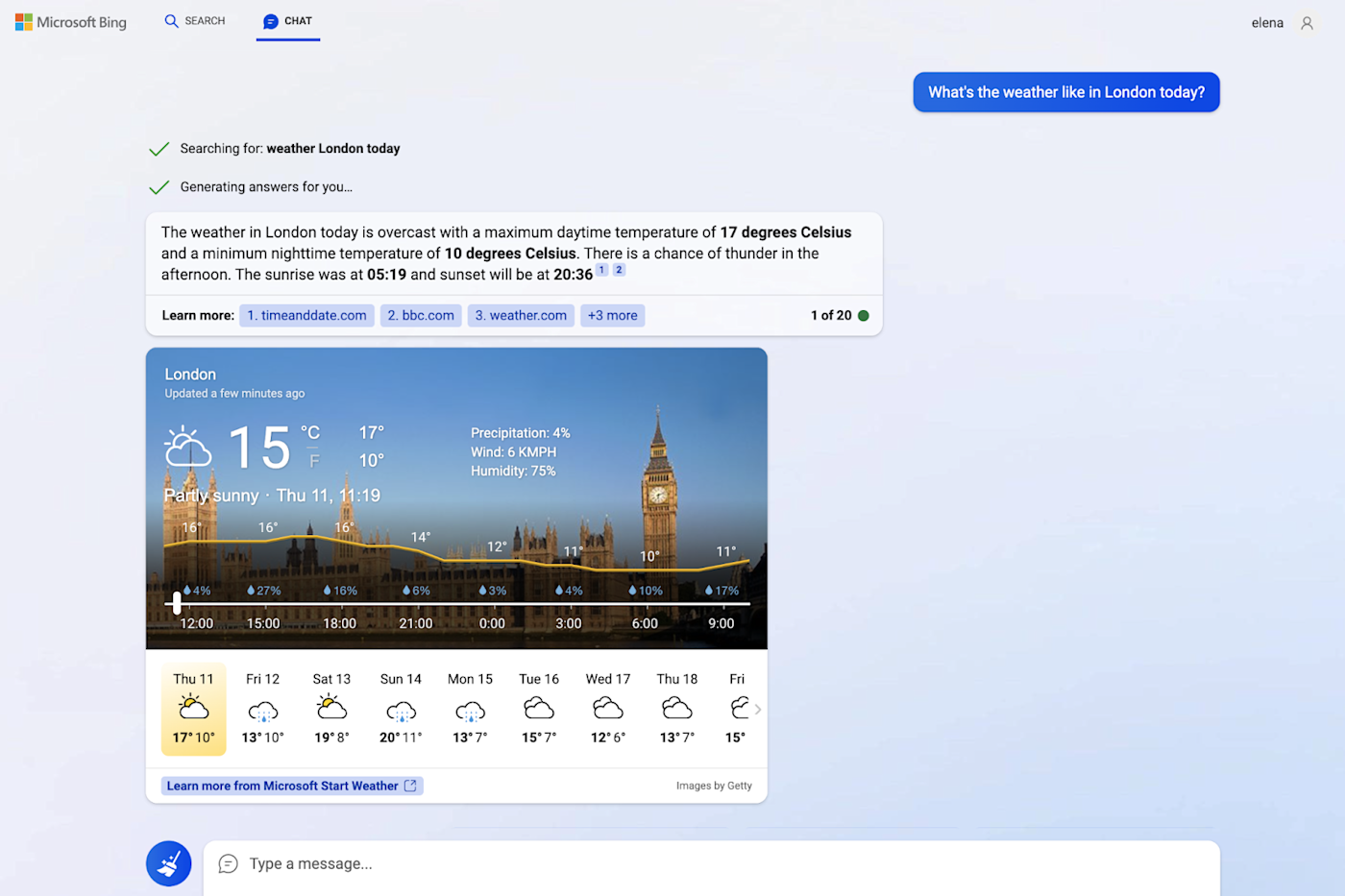
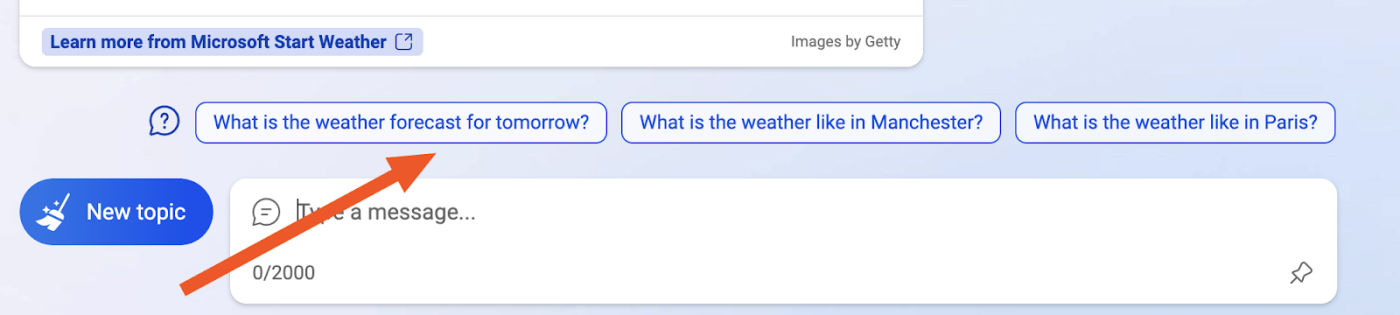
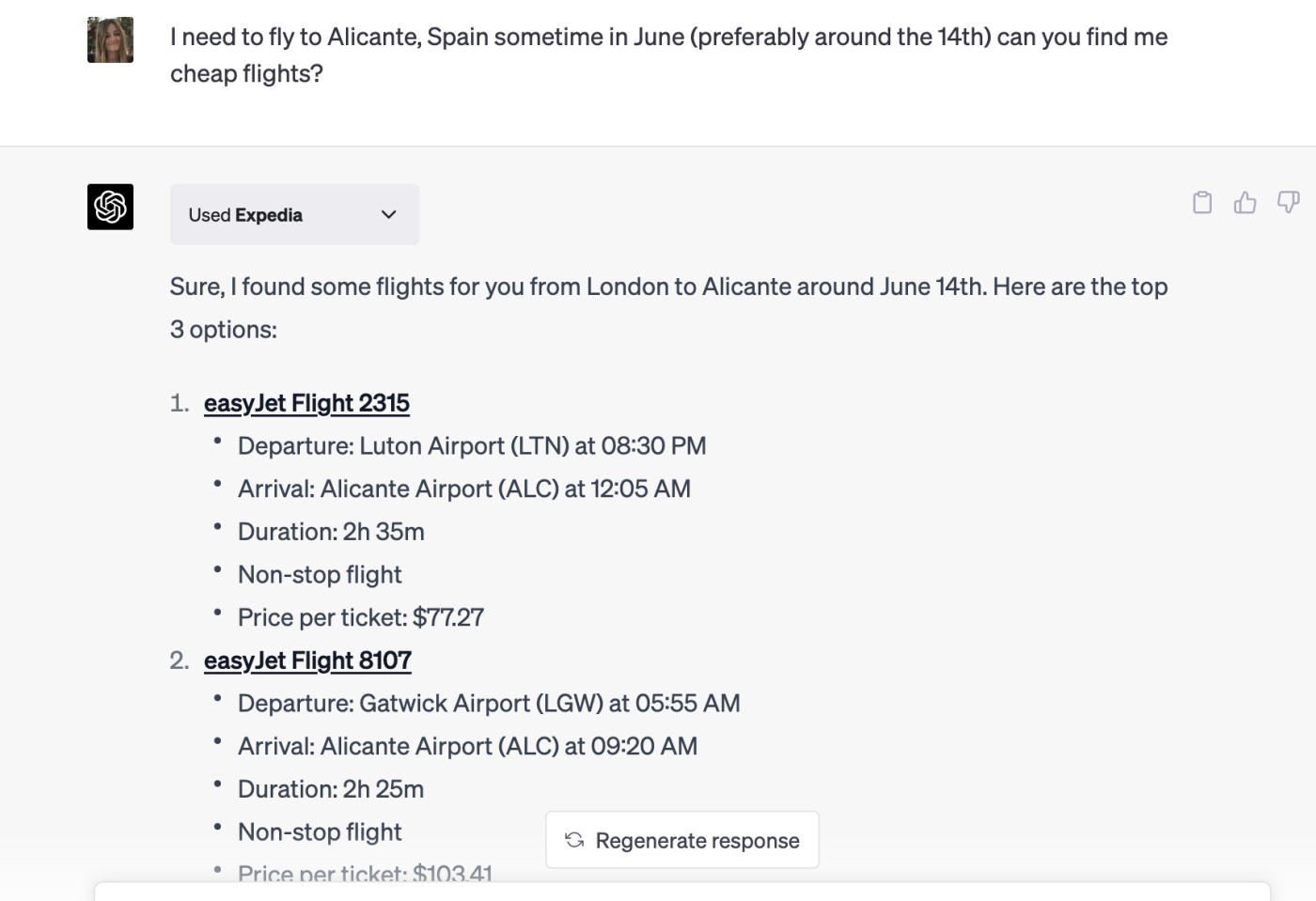
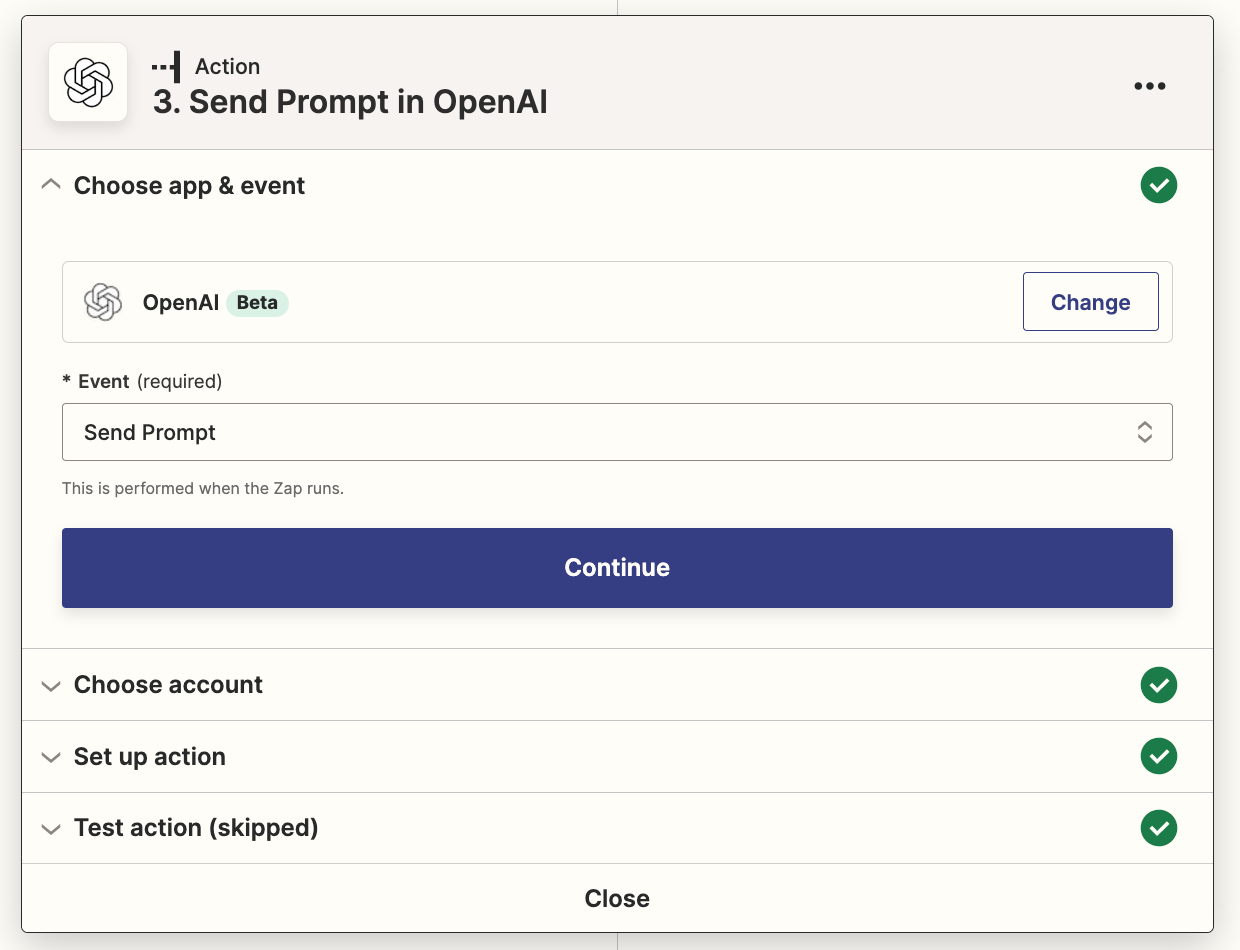
How to Assign Policy to a Group in Teams Admin Center?
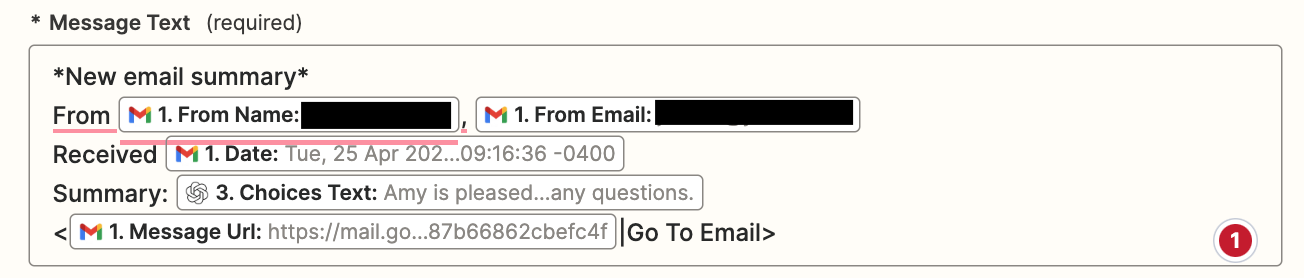
Follow the below steps to configure group policies in the Teams admin center where it majorly supports Teams calling policy, Teams call park policy, Teams policy, Teams live events policy, Teams meeting policy, and Teams messaging policy.
- Navigate using the path below.
Microsoft Teams admin center 🡢 Messaging Policies (Select the desired policy type page) 🡢 Group policy assignment 🡢 Add group 🡢 Assign policy to group
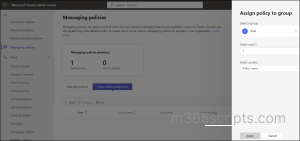
2. Then, select a group to which you want to assign a policy.
3. Set the ranking value for the group policy assignment through the select rank option.
4. After that, select a policy from the available policy types in the drop-down list and click Apply.
Unfortunately, all policy types can’t be managed under the Microsoft Teams admin center since it supports only certain policy types. Without a second thought, PowerShell is the go-to solution! Yes, managing policies using PowerShell is easy and efficient as it is the primary automation tool that ensures the deployment of objects in multiple tenants. Also, it is a place where error handling and logging are more flexible compared to the native admin center. Thus, let us deeply look through the next section of the blog to manage group policy assignments using Microsoft Teams PowerShell.
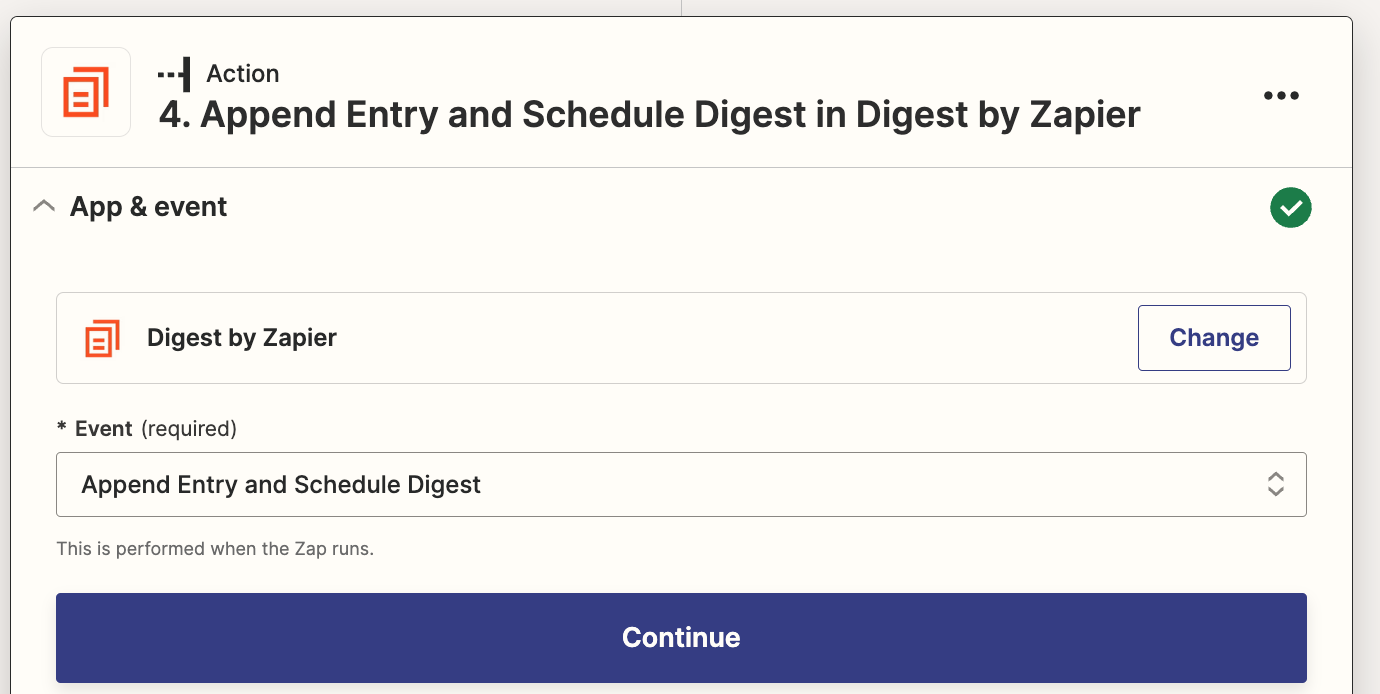
Manage Group Policy Assignments Using Teams PowerShell Module
As per the new update, Teams PowerShell Module now helps to manage group policies of Microsoft 365 groups, mail-enabled security groups, distribution lists, and security groups including Teams-related policies. Thus, create & manage groups in Microsoft 365 admin center and manage their policies in Teams PowerShell. Before getting started with PowerShell cmdlets, make sure to connect to the Teams PowerShell Module.
- Assign Policy to Group Using Teams PowerShell Module
- Get Group Policy Assignments Using MS Teams PowerShell
- Remove Policy Assignment from a Group Using TPM
- Modify Group Policy Assignment Using Teams PowerShell Module
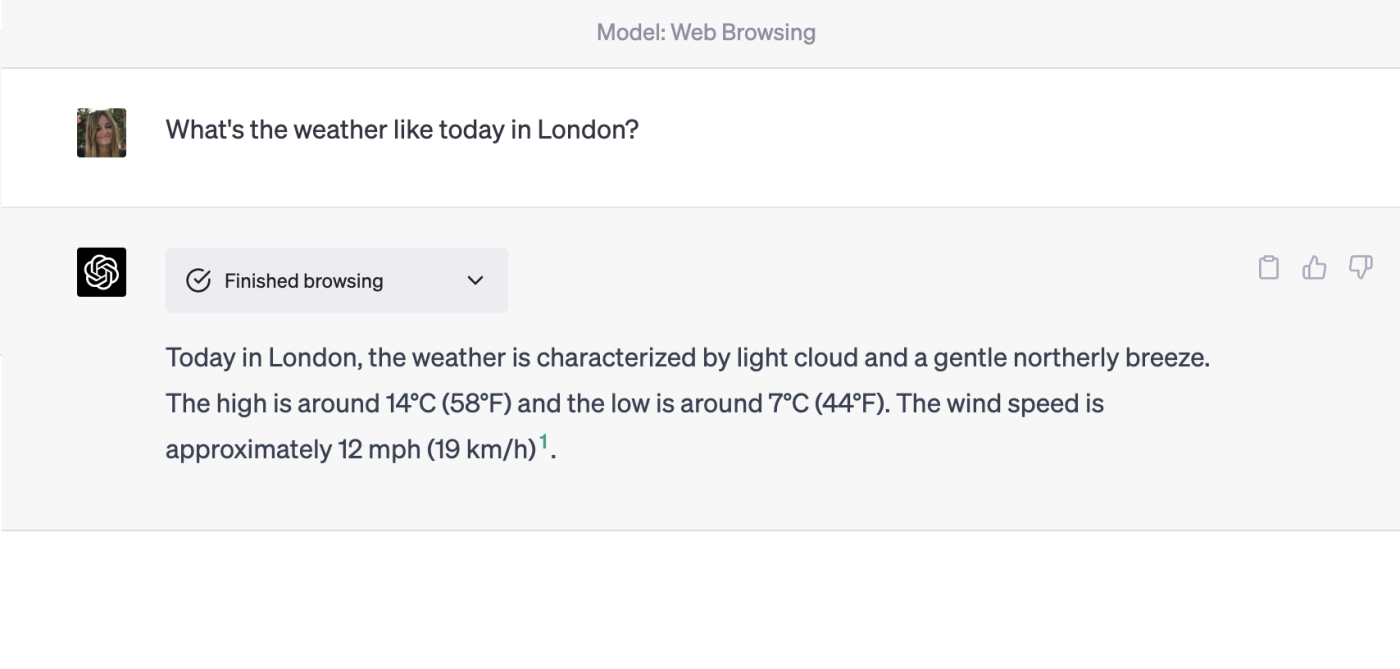
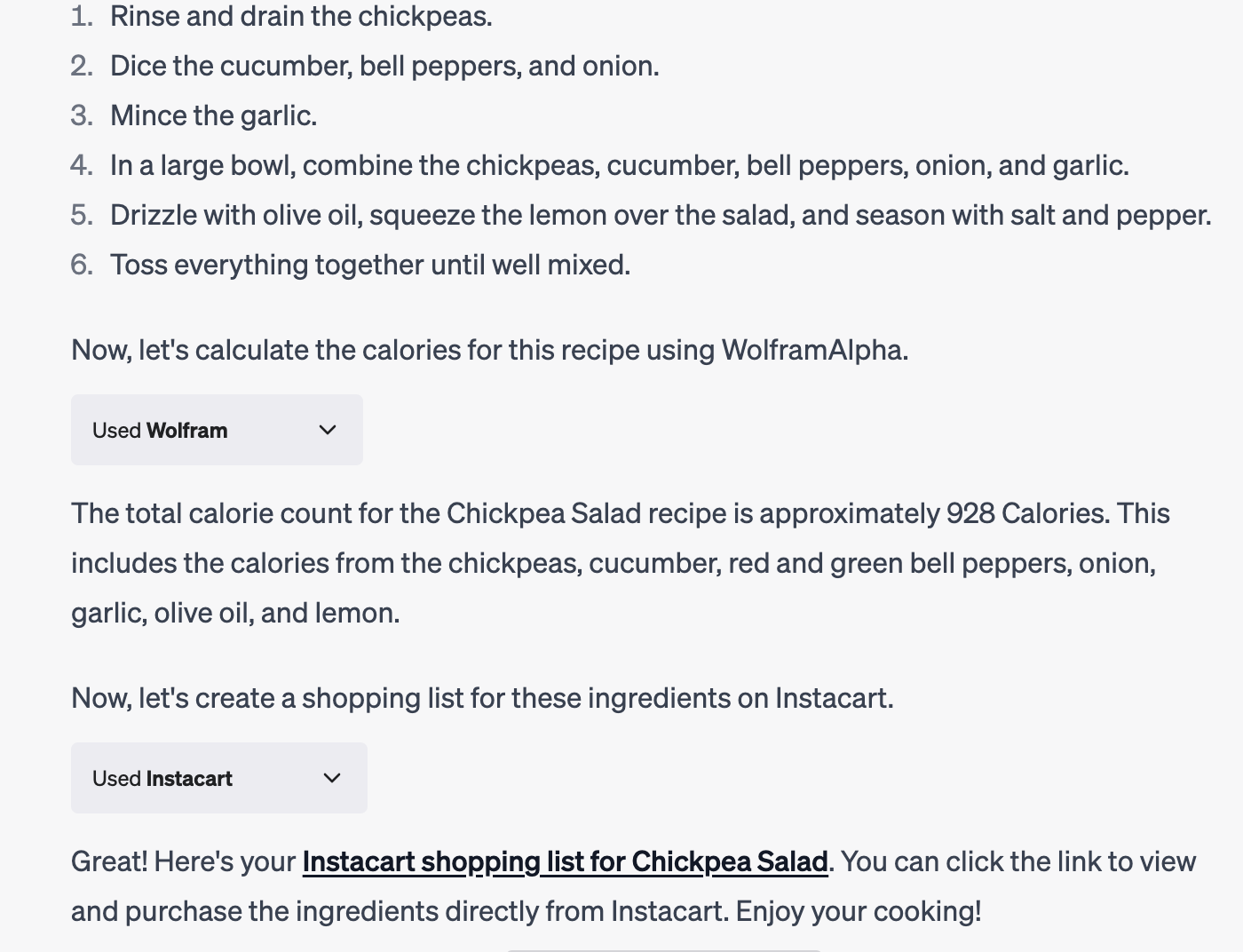
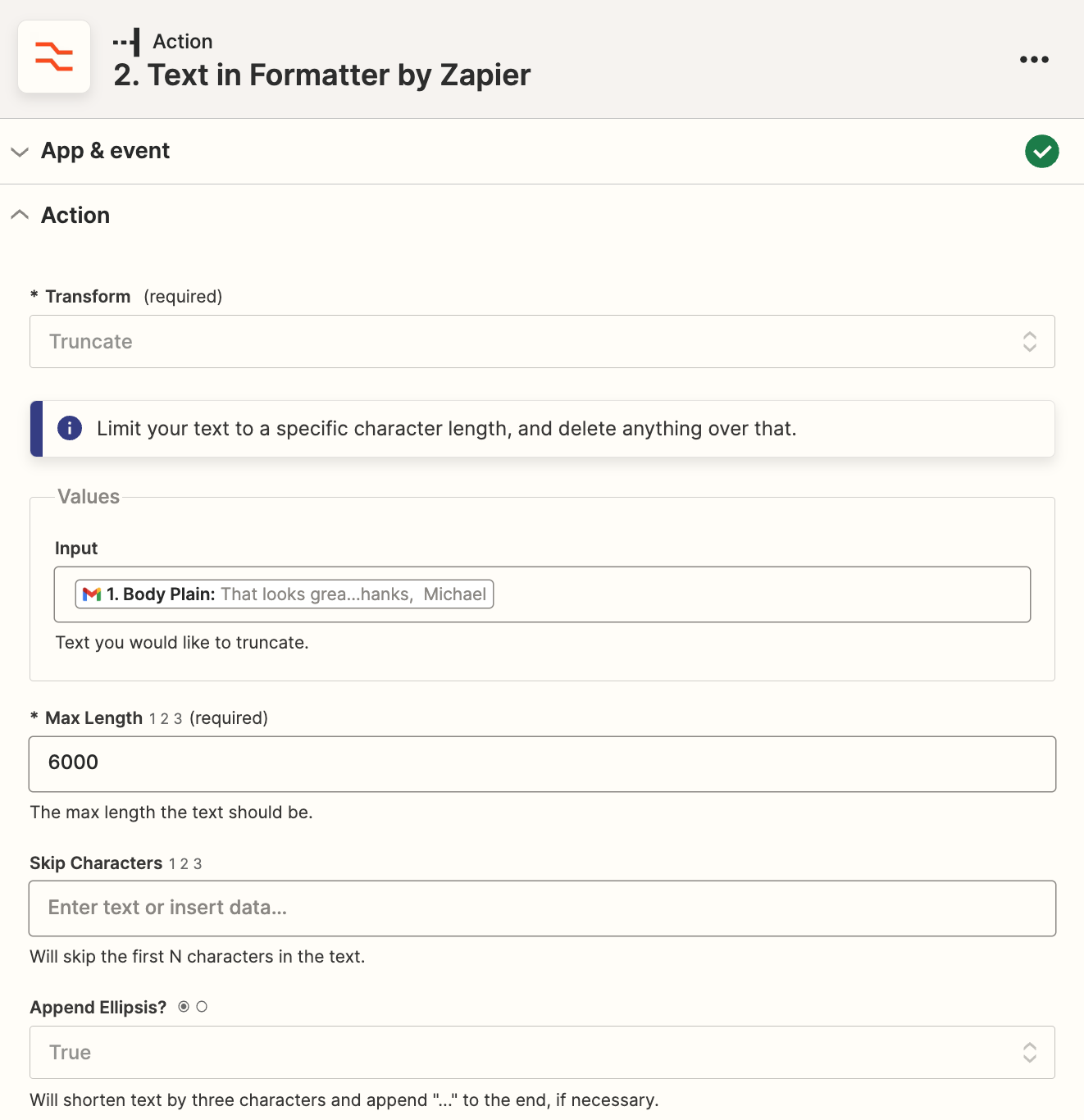
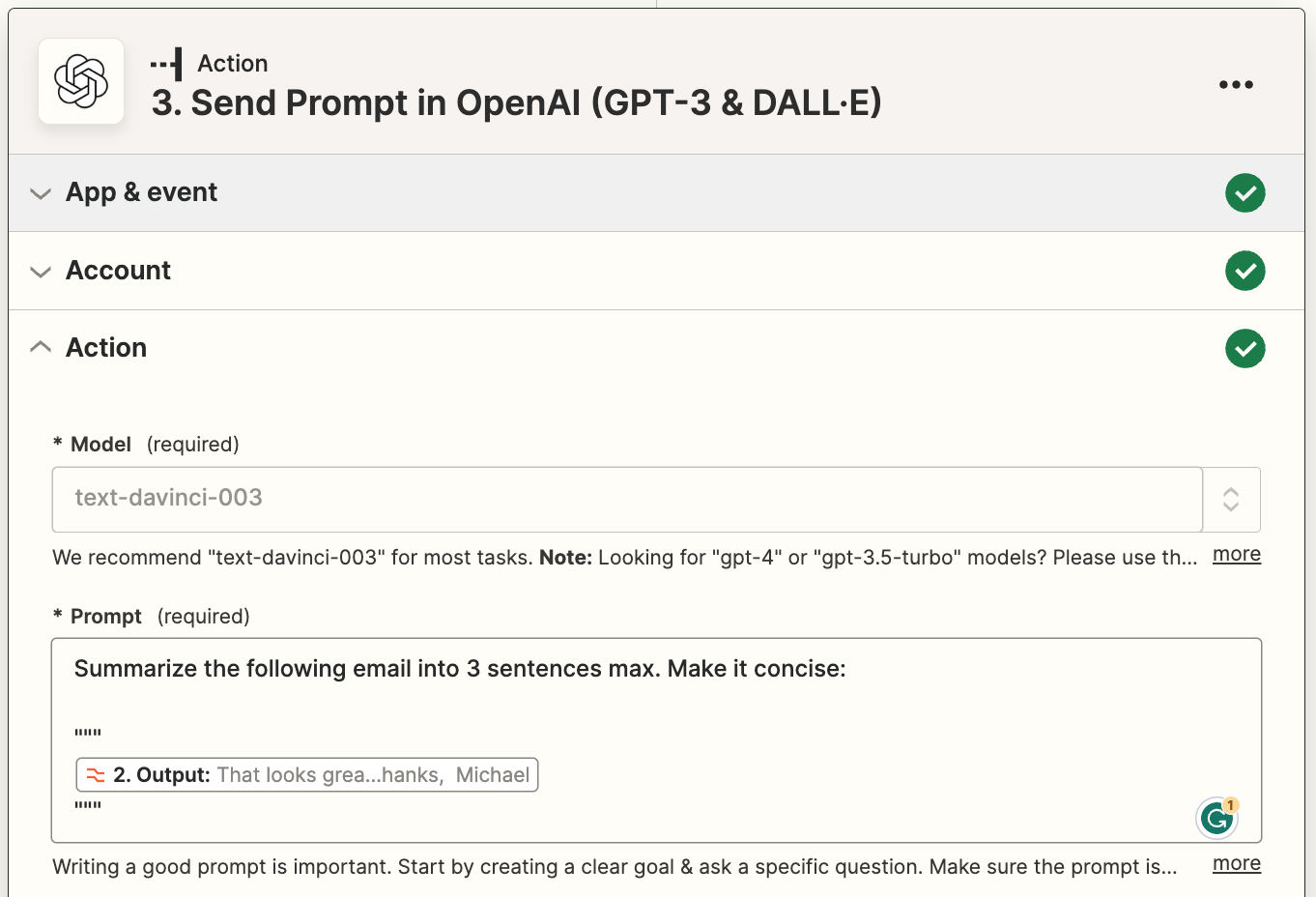
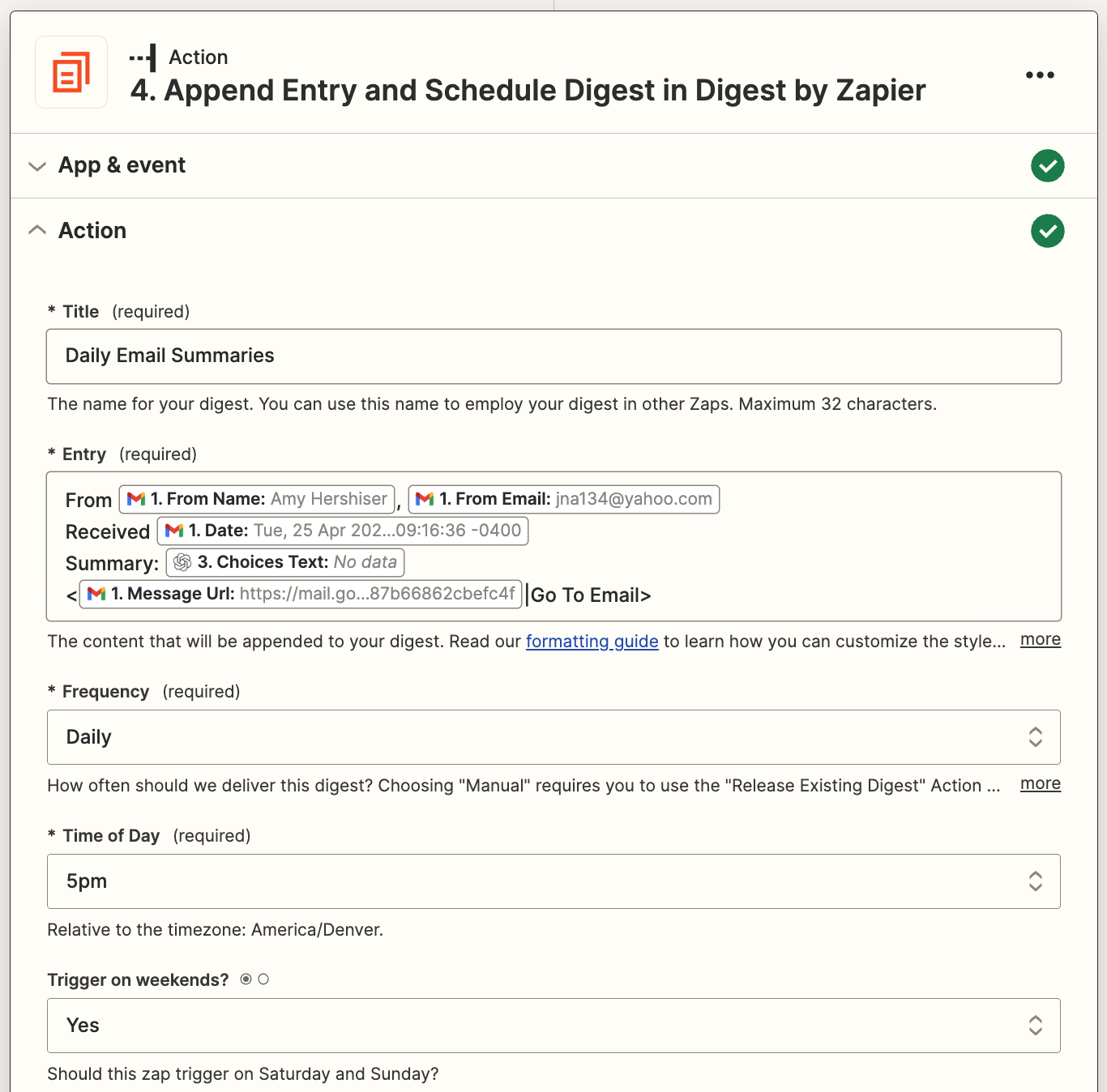
Assign Policy to Group Using Teams PowerShell Module
By defining group policies, you can control user-specific actions like allowing them to schedule meetings, edit sent messages, etc. You can assign the available policies or create and assign custom policies depending on your requirements.
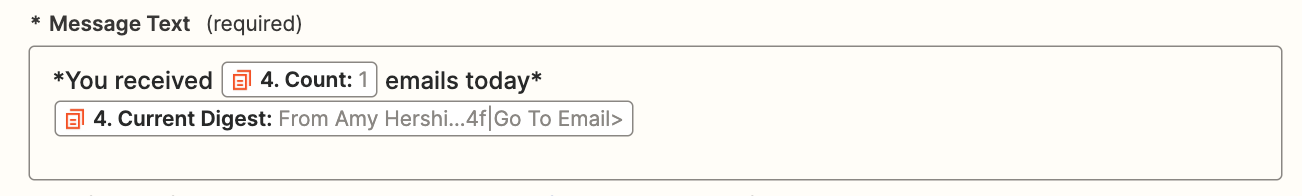
Execute the following cmdlet after replacing the unique group identifier, policy type, policy name, and expected rank to assign a new policy for a group.
New-CsGroupPolicyAssignment -GroupId d8ebfa45-0f28-4d2d-9bcc-b158a49e2d17 -PolicyType TeamsMeetingPolicy -PolicyName AllOn -Rank 1
This “New-CsGroupPolicyAssignment” cmdlet is basically used to create new policy assignments for security groups and distribution lists. In which the group ID, policy type, policy name, and rank must be mentioned as mandatory parameters. Here with the rank value as one, the ‘AllOn’ policy under TeamsMeetingPolicy type is created for the given group.
The rank of the policy must be defined to determine the precedence. The recommended group membership size is 50,000 users per group while assigning a group policy. Also, it takes 24 hours or more to propagate the policy to all members of the larger groups.
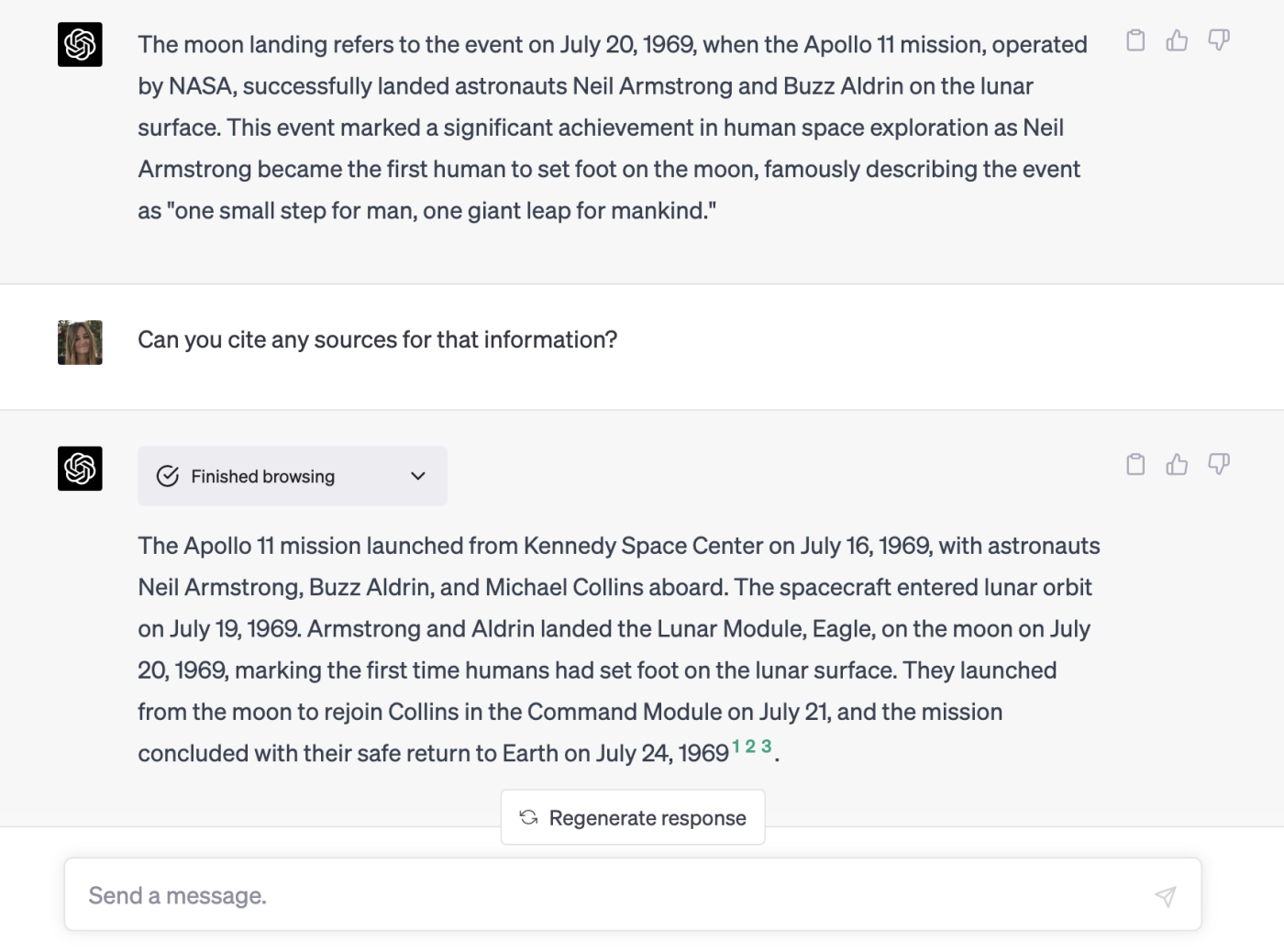
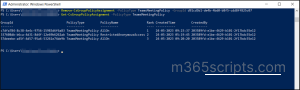
Get Group Policy Assignments Using MS Teams PowerShell
Knowing all the available policy assignments allows you to understand the working conditions and their precedence levels better. Using this you can remove unnecessary policies, alter the desired ranking for policies and efficiently manage teams & groups around your Office environment.
The “Get-CsGroupPolicyAssignment” cmdlet primarily returns all the group policy assignments with some optional parameters to filter the results.
- Primarily, list all the policy-assigned groups by running the following command.
Get-CsGroupPolicyAssignment
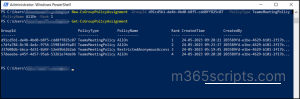
2. However, you can also retrieve all the policies assigned to a particular group using the below cmdlet.
Get-CsGroupPolicyAssignment -GroupId e050ce51-54bc-45b7-b3e6-c00343d31274
Here the cmdlet is mentioned with group ID so that retrieving only the policy assignments of that particular group.
3.Also, you can list the groups based on their policy type by executing the below command.
Get-CsGroupPolicyAssignment -PolicyType TeamsMeetingPolicy
In this case, the policy type is mentioned as TeamsMeetingPolicy. Hence this cmdlet returns only the groups assigned with this policy.
Remove Policy Assignment from a Group Using TPM
Remove the unnecessary policies found in your organization that are interrupting the ranking and slowing down the work progress. Most importantly, the removal of policies will update the ranking value of the same type policies where the policies in the list will be ranked consecutively after the removal.
Run the following cmdlet to remove a specific group policy assignment in Microsoft 365 environment.
Remove-CsGroupPolicyAssignment -PolicyType TeamsMeetingPolicy -GroupId f985e013-0826-40bb-8c94-e5f367076044
The” Remove-CsGroupPolicyAssignment” cmdlet removes the given policy type in mentioned group ID.
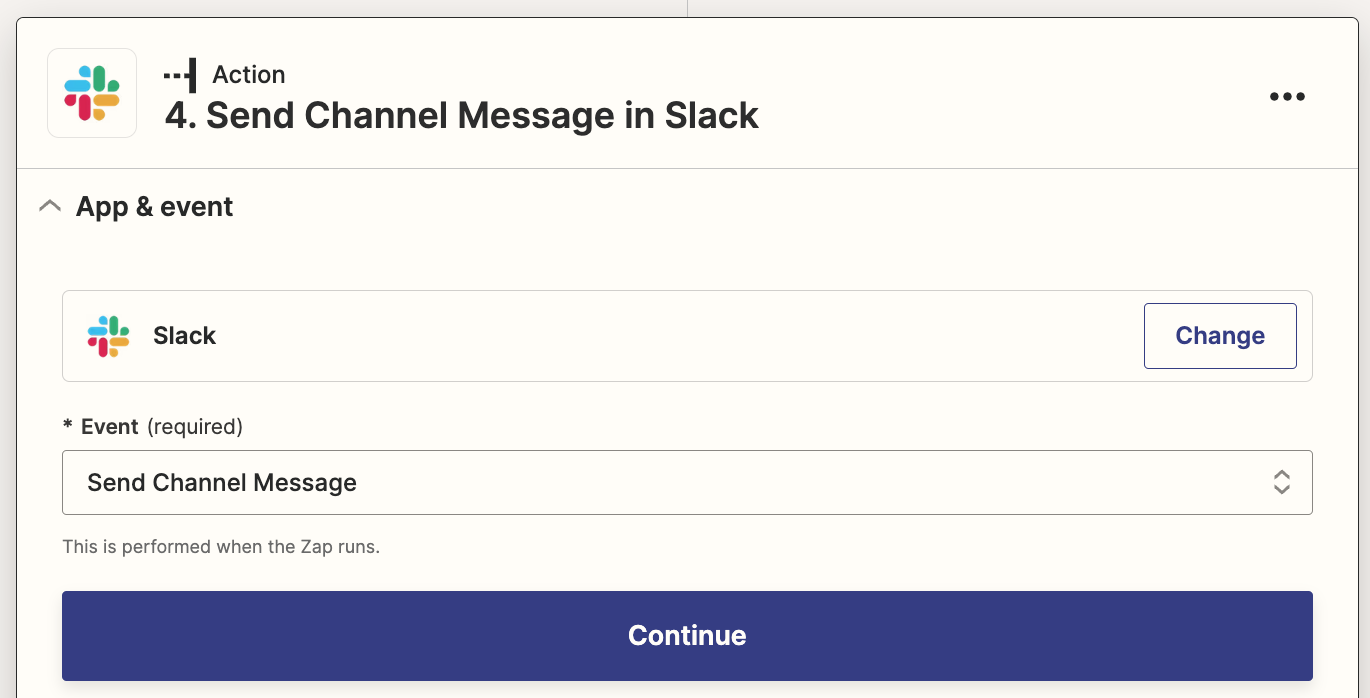
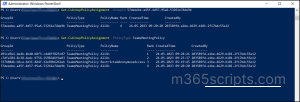
Modify Group Policy Assignment Using Teams PowerShell Module
Directly altering the policy assignment ranking value is not possible in the Teams admin center. The policy assignments should be removed and newly assigned again with a new rank value to change the ranking. To take away this hassle, PowerShell lends you a hand with a simple and reusable cmdlet which is described below.
Set-CsGroupPolicyAssignment -GroupId 566b8d39-5c5c-4aaa-bc07-4f36278a1b38 -PolicyType TeamsMeetingPolicy -PolicyName SupportCallPark -Rank 3
The “Set-CsGroupPolicyAssignment” cmdlet can be used to make the following alterations in group policy assignments based on the given attributes.
- Change policy assignment ranking.
- Change the policy under the existing policy type.
- Change policy assignment ranking value and policy of a given policy type.
In this example, the policy is changed to ‘SupportCallPark’ policy, and the rank value is assigned to 3.
NOTE: The “Set-CsGroupPolicyAssignment” cmdlet is currently not released for use. So, for now, you need to remove policies and add new policies to change the policy or ranking. But you can easily alter the policy settings once after the availability of this cmdlet.
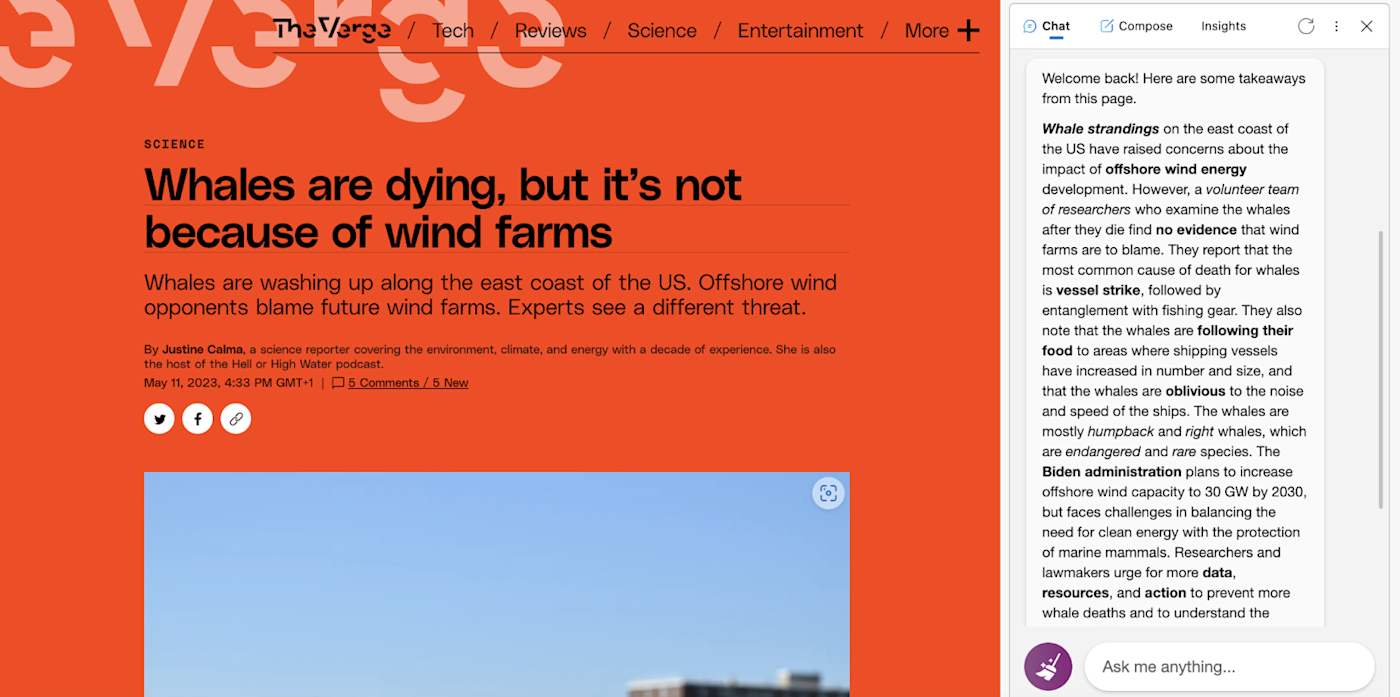
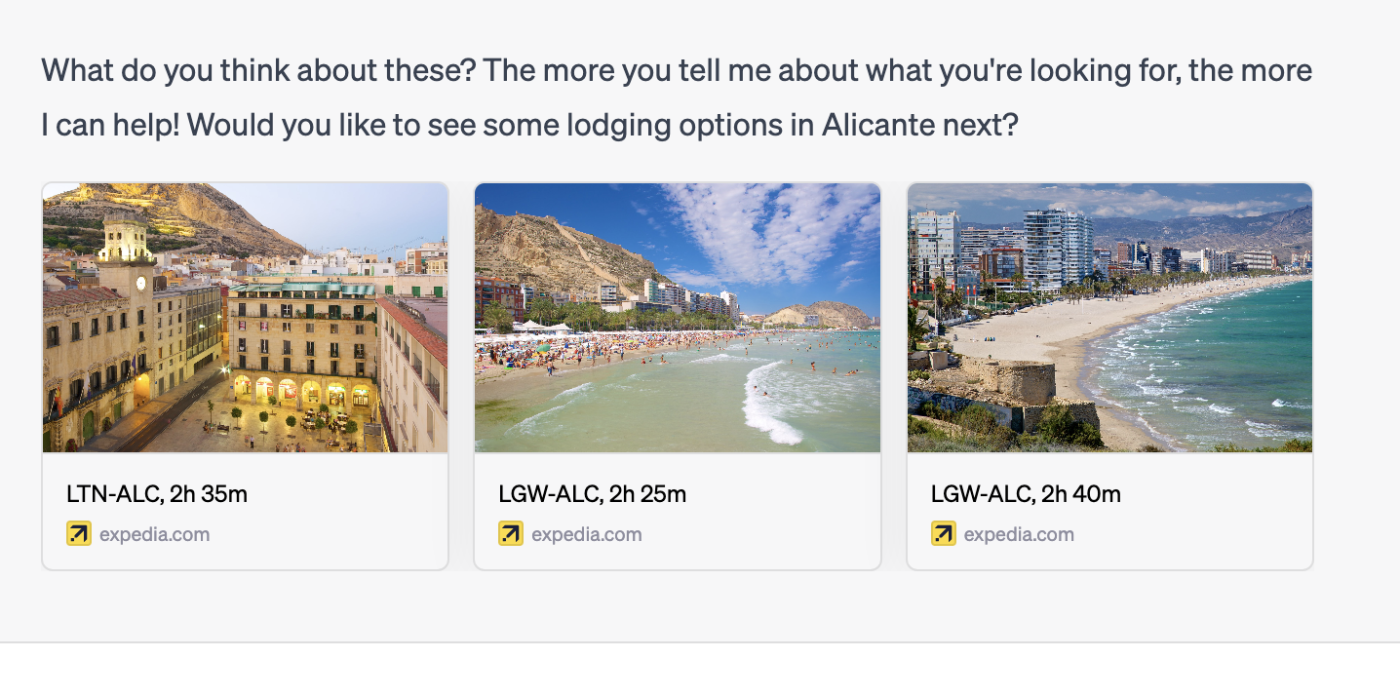
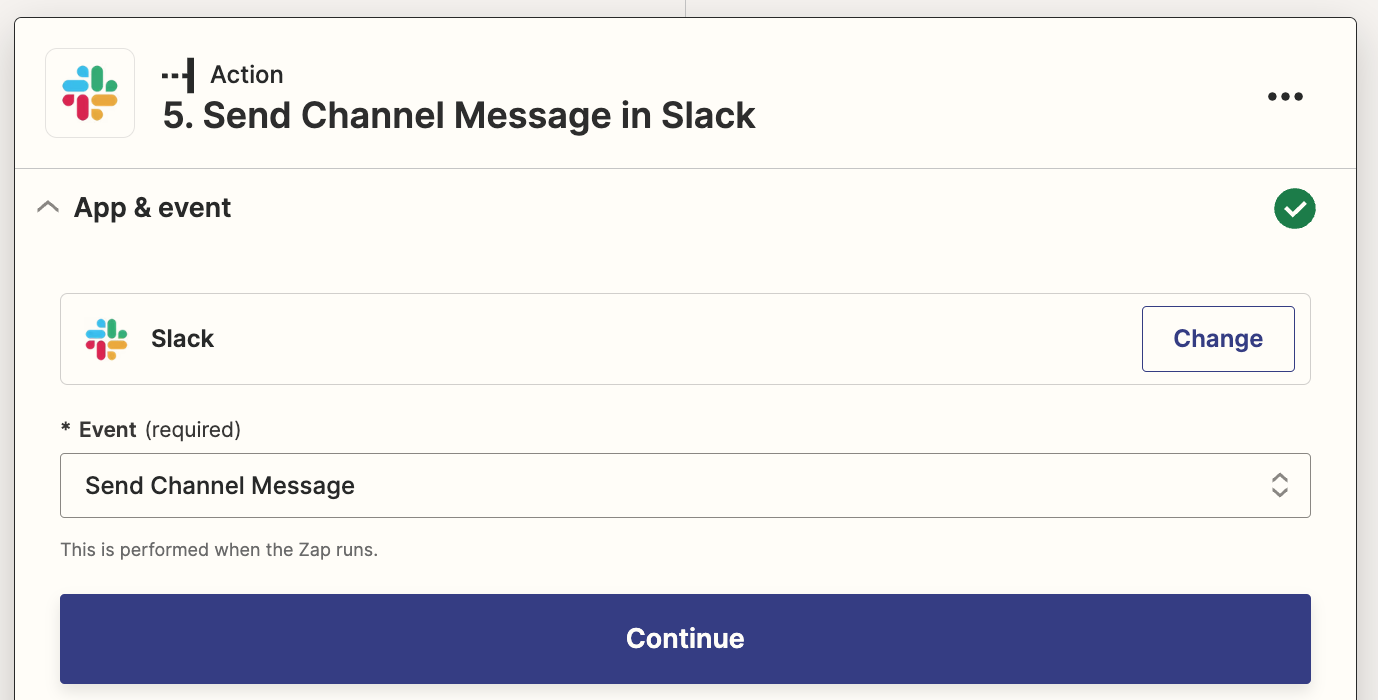
New Group Policy Assignment Support in Teams PowerShell Module
Microsoft rolls out group policy assignment support for additional policies in Teams PowerShell Module as a new update. So that admins can manage their groups in the M365 admin center and group policies in Teams PowerShell with a breeze. This feature will allow you to configure custom policies to groups for all Microsoft commercial licenses. With this update, dependency on global or direct policy assignments through manual methods is eliminated. In addition to the core policies such as meeting policies, calling policies, and messaging policies, the following policies are now expected to be available in Teams PowerShell by late May 2023.
- Application Access Policy
- Call Hold Policy
- Carrier Emergency Call Routing Policy
- Cortana Policy
- Dial Out Policy
- Education Assignments App Policy
- Emergency Calling Policy
- Enhanced Encryption Policy
- Events Policy
- External Access Policy
- Feedback Policy
- Files Policy
- IPPhone Policy
- Media Logging Policy
- Meeting Branding Policy
- Meeting Template Permission Policy
- Mobility Policy
- Notification And Feeds Policy
- Room Video Tele Conferencing Policy
- Synthetic Automated Call Policy
- Teams Branch Survivability Policy
- Template Permission Policy
- VDI Policy
- Video Interop Service Policy
- Voice Routing Policy
- Voicemail Policy
In conclusion, ultimately manage all group policies including Teams using PowerShell cmdlets. Take charge of the user-specific actions and security controls through this group policy assignment. Not only policies, you can also manage your Teams using PowerShell for effective administration. Rather than performing numerous repetitive tasks in the Teams admin center, automate them with just a few cmdlets in PowerShell.
I hope that this blog provides you with deeper insights into group policy assignments using Teams PowerShell. For any clarifications feel free to reach us through comments.
Source :
https://m365scripts.com/microsoft365/group-policy-assignments-using-microsoft-teams-powershell/