This article explains how you can disable Cortana in Windows 11 using different methods. You can disable the Cortana in Windows 11 or even uninstall it if you don’t use it.
Cortana in a cloud-based assistant by Microsoft that assists users with voice commands. Cortana in Windows has a chat-based UI that gives you the ability to interact using typed or spoken natural language queries.
In the latest update to Cortana in Windows, you can search for documents and compose quick emails. You can also invoke the app using the wake word “Cortana.” Cortana can also launch Alexa app on Windows 10 (if it’s already installed).
Note that you must sign in with your Microsoft account to use Cortana app. To learn about Cortana in detail, refer to the Microsoft documentation on Cortana.
Table of Contents
- What can you do with Cortana in Windows 11?
- Why Disable Cortana in Windows 11?
- Method 1 – Turn off Cortana from Windows 11 Settings
- Method 2 – Disable Cortana using Task Manager on Windows 11
- Method 3 – Disable the Cortana from Registry Editor
- Method 4 – Disable Cortana using Group Policy (GPO)
- Method 5 – Uninstall Cortana in Windows 11 using PowerShell
- Method 6 – Disable Cortana using Intune (MEM)
- How To Reinstall Cortana App in Windows 11
- Conclusion
What can you do with Cortana in Windows 11?
Here are some of the things you can do with Cortana in Windows 11:
- Calendar and Schedule Assistance – Check your calendar, know the meeting schedule etc.
- Meeting Help – Join Teams meetings, find what’s the next meeting is and with whom, book a meeting with your colleague in the organization etc.
- Find out about people in your organization – Cortana can help you learn about people in your organization
- Make lists and set reminders and alarms – You can ask Cortana to create a new list or add something to a list you already have
- Launch Apps – With voice commands, the Cortana can launch the apps installed on your Windows. For example, you can launch Word app, Calculator etc.
- Get definitions and quick answers
- Get weather and news updates – You can get the weather information and new updates using Cortana. This is very similar to news and interests widget that offers a quick overview of key headlines and weather information relevant to you.

Why Disable Cortana in Windows 11?
If Cortana is so useful, then why disable it? The answer is not all the Windows users like Cortana because it’s not accurate all the time and the app consumes a lot of system resources.
In addition, most users can simply work without using Cortana in daily routine. If you open Microsoft Store and read the Cortana app reviews, the users have expressed concerns about this app. The Cortana app in Microsoft Store has an overall rating of 1.8/5 which doesn’t seem good.
Plus Cortana collects your personal information, search history, email information and stores it on cloud which for some users is not ok.
In Windows 11, Cortana is still present, but it’s no longer part of the first boot experience. However, in Windows 11, you can turn off Cortana if you don’t like it or even uninstall it completely.
There are multiple ways to disable Cortana in Windows 11. This article covers different methods to temporarily or permanently disable Cortana as well as fully uninstall Cortana from Windows 11.
To summarize, we will use the following methods to disable the Cortana in Windows 11:
- Using Windows 11 Settings
- Using Task Manager in Windows 11
- Disable Cortana using Group Policy
- Use PowerShell commands to disable Cortana
- Intune or Microsoft Endpoint Manager
- Configuration Manager
Method 1 – Turn off Cortana from Windows 11 Settings
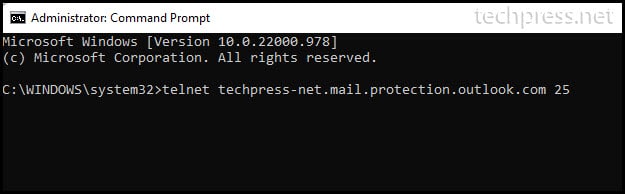
You can turn off the Cortana from Windows 11 settings with following steps. Click Start and launch the Windows 11 Settings app. You can use the shortcut command Win+I to directly launch the settings app.
From the list of settings, select Apps and then select Apps & Features.

On the Apps & Features window, you should find all the apps installed on Windows 11. From the App list, search for Cortana app. Once the Cortana app appears in the listing, click on the vertical dots and select Advanced Options.

The advanced options for Cortana displays additional settings to manage the app. Under Runs at log-in, turn off the Cortana. By moving the slider to off, you disable Cortana in Windows 11.
Note that the above step temporarily disables the Cortana app in Windows 11. The user can manually turn on the Cortana app whenever required.

Method 2 – Disable Cortana using Task Manager on Windows 11
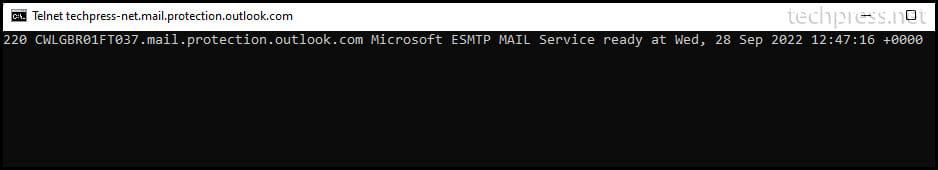
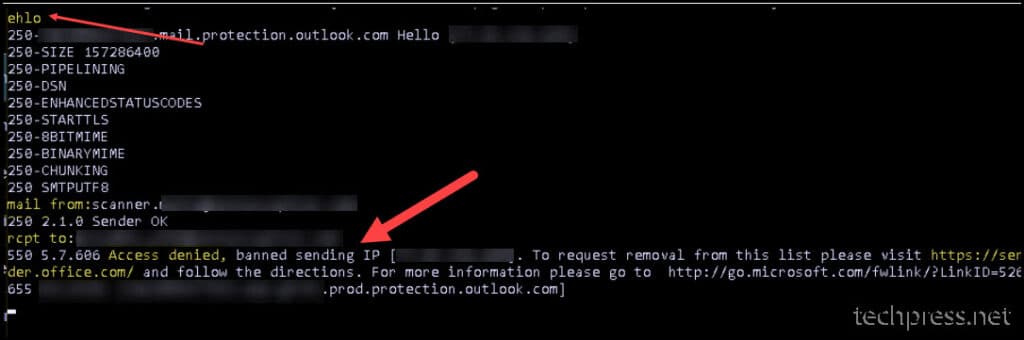
In Windows 11, you can quickly disable Cortana using the task manager:
- On Windows 11, use the shortcut keys Ctrl+Shift+Esc to launch the task manager.
- When the task manager opens, click the Startup tab.
- From the list of start up apps, click the Cortana app and select Disable button.
- You may also right-click Cortana and choose the Disable option.

Method 3 – Disable the Cortana from Registry Editor
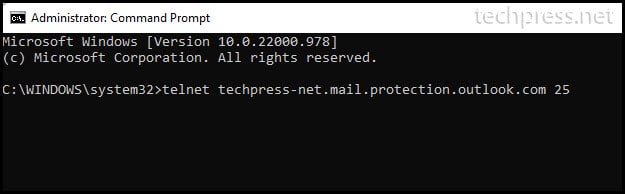
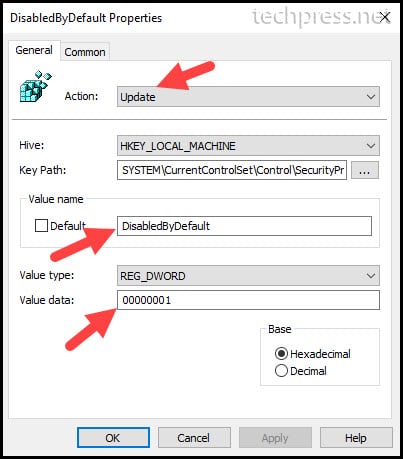
You can permanently disable Cortana in Windows 11 by editing the registry. Before you modify the registry, either create a system restore point or backup the entire registry.
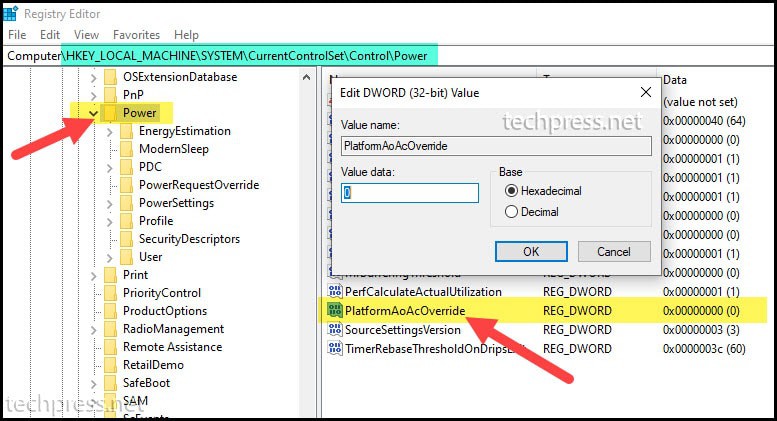
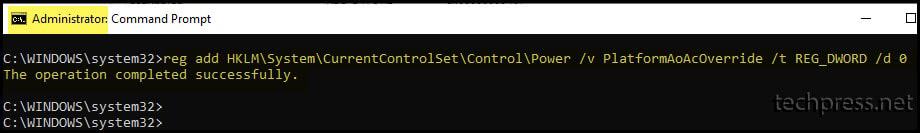
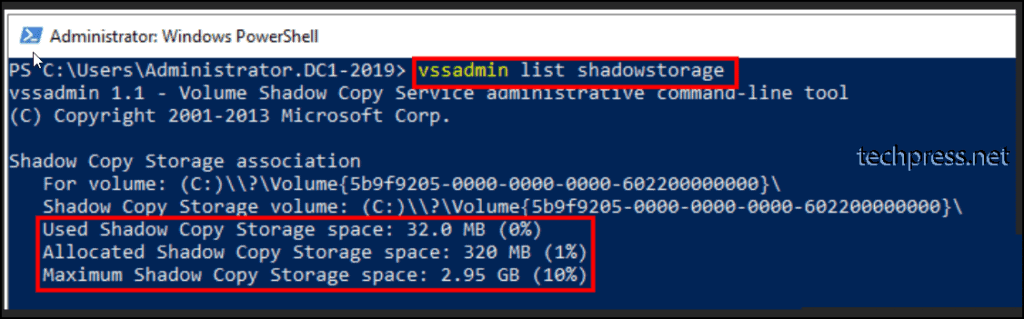
Launch the Registry editor on Windows 11 by running the command regedit. Once the registry editor opens, go to the following registry path.
Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\Windows Search
If you don’t find the Windows Search key, you must create a new key. Let’s start by creating a new key under Windows and name it as Windows Search.
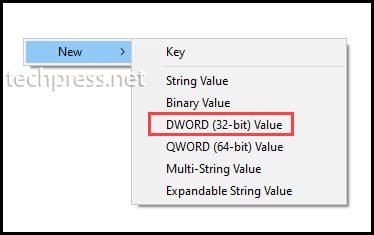
Right click Windows Search key and select New > DWORD (32-bit) Value.

Enter the value name as AllowCortana and the value data is 0. By setting the AllowCortana value to 0, you disable Cortana in Windows 11. Click OK to save the changes.

After making the above changes to registry, restart Windows 11 PC. Log in to Windows 11 PC and launch the Cortana app. You should see the following message “Cortana is disabled. To use Cortana you need to get permission from your administrator“. This confirms the Cortana app is disabled on Windows 11.

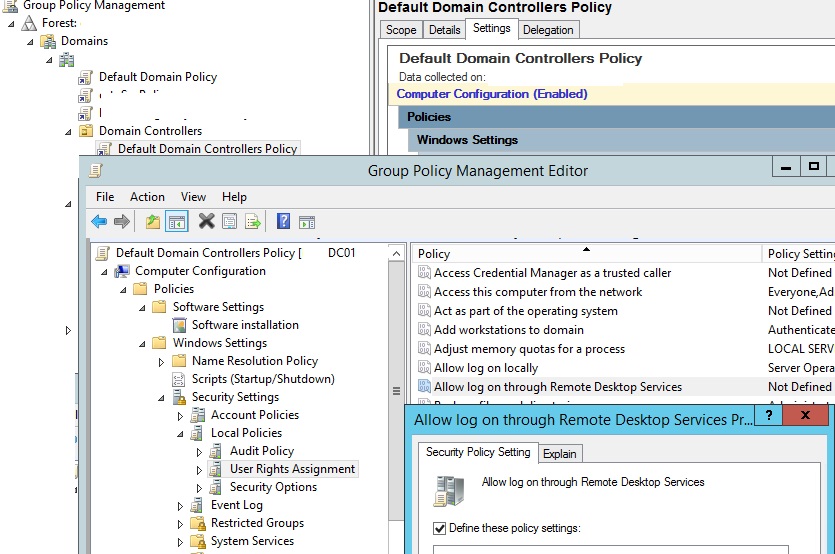
Method 4 – Disable Cortana using Group Policy (GPO)
You can disable Cortana permanently in Windows 11 using Group Policy. The Group Policy method is useful when you want to disable the Cortana access on domain joined Windows 11 PCs.
When you want to disable Cortana on multiple Windows 11 computers that are joined to an Active Directory domain, the group policy is the best option.
Before you create a GPO to disable Cortana, have few devices for testing purpose. It is not recommended deploying a GPO directly to production servers and workstations.
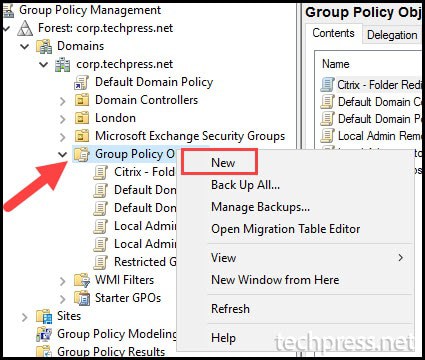
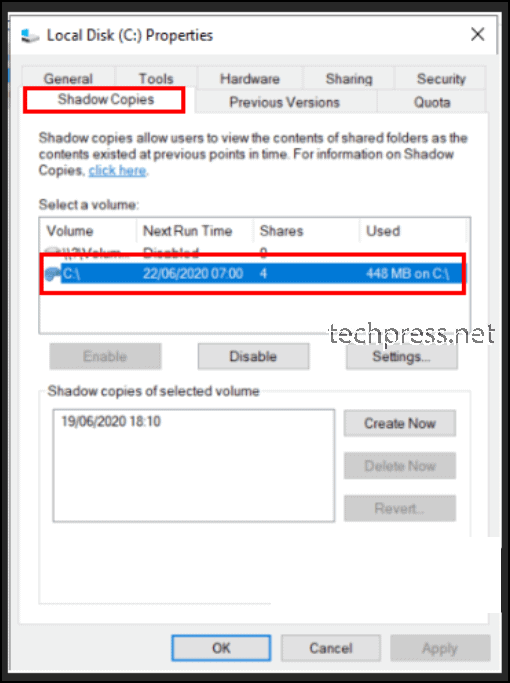
Let’s create a new GPO to disable Cortana in Windows 11. Log in to a domain controller or a member server installed with GPMC. Launch the Group Policy Management Tools from Server Manager > Tools.
Once the Group Policy Management console is launched, expand the domain and right-click Group Policy Objects and select New.
Note: We are going to create a new GPO which should then be linked to an OU later.
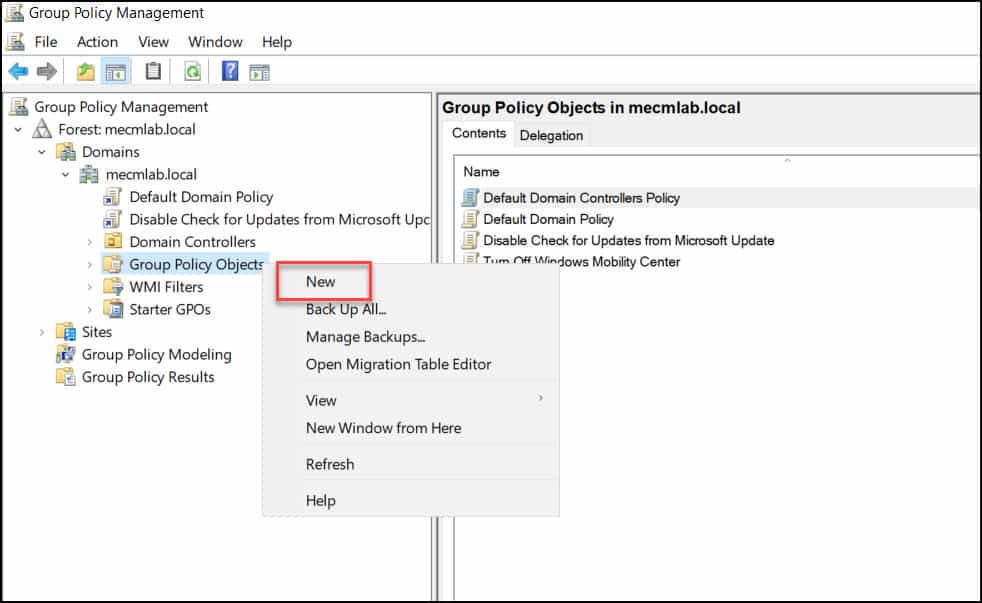
Specify the GPO name as Disable Cortana or something similar and click OK.

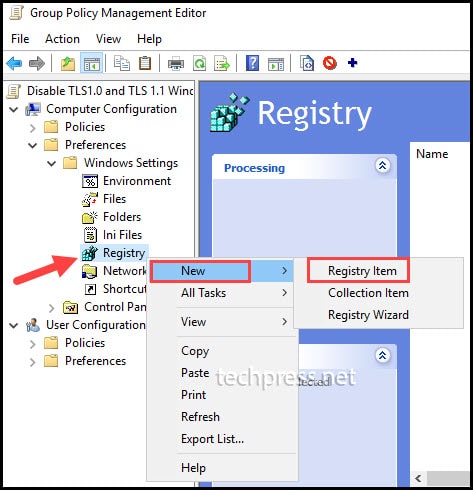
In the Group Policy Management editor, navigate to following settings Computer Configuration > Administrative Templates > Windows Components > Search.
From the list of policy settings, right-click the setting named “Allow Cortana” and select Edit. The Allow Cortana policy settings include:
- This policy setting specifies whether Cortana is allowed on the device.
- If you enable or don’t configure this setting, Cortana will be allowed on the device. If you disable this setting, Cortana will be turned off.
- When Cortana is off, users will still be able to use search to find things on the device.
Set Allow Cortana to Disabled. With the selected setting, you disable the Cortana on Windows 11. Click Apply and OK.

After following the above steps, in the GPMC console, right-click the OU that you want to target the GPO and select Link an existing GPO and select the Disable Cortana GPO.
Once you have linked the GPO to a OU or to an entire domain, the computers will download the policy based on the Group Policy refresh interval. The Group Policy refresh interval for computers policy lets you specify how much the actual update interval varies.
Read: How to modify the Group Policy Refresh Interval
After the Disable Cortana GPO is successfully applied to the domain computers, the access to Cortana app will be disabled for Windows 11.
Method 5 – Uninstall Cortana in Windows 11 using PowerShell
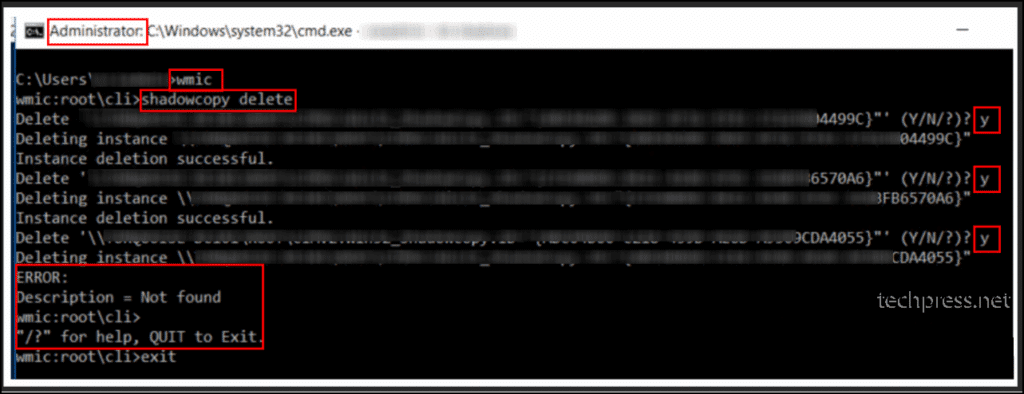
If you have decided to uninstall Cortana from Windows 11, you can do it using PowerShell:
- On Windows 11 PC, launch the PowerShell as administrator.
- Paste the following command in the PowerShell window and press Enter key.
- Get-AppxPackage -AllUsers Microsoft.549981C3F5F10 | Remove-AppPackage.
- The above PowerShell cmd uninstalls the Cortana from Windows 11 for all users.

Note: You don’t have to reboot the computer after uninstalling Cortana.
Method 6 – Disable Cortana using Intune (MEM)
Using Intune, you can easily disable Cortana on Windows 11 managed PCs using Configuration Profiles. The Intune Catalog settings lets you define the settings to disable the Cortana access on Windows 10 and Windows 11 devices.
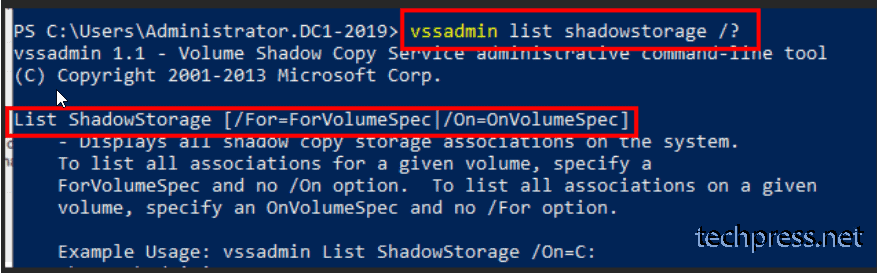
Let’s see how to disable Cortana using Intune. First sign-in to the Intune Portal (Microsoft Endpoint Manager admin center). Go to Devices > Windows > Configuration Profiles. Select Create Profile.

When you create a profile in Intune, you specify the Platform and Profile Type. In this example, select the Platform as Windows 10 and later and Profile Type as Settings Catalog. Click Create.

On Create Profile Basics tab in Intune portal, enter the name of the profile to “Disable Cortana Access” or “Turn off Cortana“. Enter a brief description about the profile and click Next.

On the Configuration Settings tab, we will use settings catalog in Intune to define the settings to turn off Cortana. Select +Add Settings.

The Settings picker window gives you an option to search for the correct keywords or terms related to settings. Enter the search term as “Cortana” and click Search button.
From the list of search results, click the Experience category and now select the Setting name – Allow Cortana.

- Allow Cortana – Specifies whether Cortana is allowed on the device. If you enable or don’t configure this setting, Cortana is allowed on the device. If you disable this setting, Cortana is turned off. When Cortana is off, users will still be able to use search to find items on the device.
By default, the Allow Cortana setting is set to “Allow“. To disable the Cortana on Windows 10 and Windows 11 devices, set the Allow Cortana setting to “Block“. By setting the Allow Cortana to Block, you disable the Cortana on endpoints.
Click Next to continue.

On the Assignments tab, click Add Groups to include the group of devices on which you want to disable Cortana. Click Next to continue.

Scope tags are optional, but you may define them if required. I am going to skip and click Next.

On the Review + Create tab, take a final look at the settings that you defined so far. If it’s all good, click Create.

After you create the policy, a notification will appear automatically in the top right-hand corner with a message. Policy Created – “Disable Configure Access” created successfully. The policy is also shown in the Configuration profiles list along with other profiles.
After you deploy the policy, the assigned groups will receive the profile settings once the devices check-in with the Intune service.
To monitor the Intune policy assignment, from the list of Configuration Profiles, select the policy and here you can check the device and user check in status. If you click View Report, additional details are displayed.

Once the devices receive the policy settings from Intune, log in to one of the devices and launch Cortana. Now you should see Cortana is disabled message. This confirms that you can disable the Cortana access using Intune on your Windows devices.

How To Reinstall Cortana App in Windows 11
If you have uninstalled Cortana app from Windows 11 using any of the above methods and want to reinstall it, the process is simple.
To reinstall the Cortana app, launch the Microsoft Store app in Windows 11. Search for Cortana app in Microsoft Store and click Get. The latest Cortana app will be downloaded and installed on the Windows 11 PC.

Conclusion
Disabling the Cortana from Windows 11 is optional. If you are not going to use Cortana app, you can easily disable it with any of the methods covered in this post.
Source :
https://www.prajwaldesai.com/best-ways-to-disable-cortana-in-windows-11/










.jpg)