30.07.2023
Post-COVID-19, with the rise of remote work, business network security has become paramount. The rapid shift to remote work unveiled numerous network vulnerabilities, risking data breaches, financial losses, and reputational harm.
No longer is a simple firewall enough; today’s remote security includes technologies from VPNs to cloud measures and the zero-trust model. Besides these tools, it’s crucial to recognize risks, such as shared passwords, outdated software, and insecure personal devices.
Here are some of the best tips to enhance your business’s remote security, guaranteeing safe and streamlined operations.
What is Business Remote Network Security?
Business remote network security encompasses measures safeguarding a company’s digital assets accessed from remote locations. Securing these connections has become paramount with the growth of remote work and evolving digital landscapes.
Who is Responsible for Remote Network Security?
The responsibility for ensuring that your remote network stays secure primarily rests with SecOps. They can combat cybersecurity risks via strong access controls, monitor remote access, update rules, and test remote access operations.
Cybersecurity teams now lead and manage secure remote access policies, processes, and technologies, though traditionally, it’s a network team’s role.
SecOps has gained prominence amid increasing cyber threats and a remote workforce. Their roles include:
- Sharing passwords
- Usage of software that breaches an organization’s security standards
- Personal devices without encryption
- Negligible or absent patching practices
Key attributes of a proficient SecOps team include:
- Diverse expertise: SecOps teams boast a mix of professionals.
- Advanced tools: They use cutting-edge tools for real-time monitoring and quick threat detection and response.
- Cloud security management: Secure and manage cloud resources.
- Automation and AI integration: Use automation and AI to address modern threats quickly.
- Adherence to best practices: SecOps teams follow best practices, staying proactive against emerging threats.
How Does Remote Network Security Work?
Remote network security allows users to access resources anywhere without risking data or network integrity.
- The basics of remote access: Users must install the remote software on the target devices. Once active, users log in, choose the target device, and its screen gets mirrored.
- Securing endpoints: Secure all endpoints (PCs, smartphones) on networks with updated antivirus and adherence to security guidelines. Equip employees with tools and knowledge for protection.
- Minimizing attack surfaces: Remote access, while convenient, introduces vulnerabilities. Ransomware, for example, frequently targets remote desktop protocols (RDP). It’s essential to configure firewalls to respond only to known IP addresses.
- Implementing multi-factor authentication (MFA): MFA enhances security with multiple identifiers like passwords and tokens, granting access to verified users only.
- Using VPNs: VPNs secure connections on public Wi-Fi but update software to prevent vulnerabilities.
- Monitoring and logging: For remote work, update SIEM and firewall to handle home logins. Record and monitor all remote sessions in real-time, triggering alerts for suspicious activity.
- User education: Informed users significantly bolster cyber defenses. Employees require training to spot threats.
- Policy updates and role-based access control (RBAC): Updating policies across all devices is vital. Also, it’s important to grant access based on roles.
Why is Remote Network Security Important?
Robust remote network security is essential as businesses embrace remote work’s benefits, like flexibility and cost savings, while facing significant cybersecurity challenges.
Protecting data and operations in remote work is vital for business continuity and reputation. Companies must prioritize safeguarding digital assets and networks from threats and breaches.
- Unprecedented growth in remote work: Over the last 5 years, remote work has grown by 44%, challenging traditional corporate network security perimeters as operations expand online.
- Vulnerability to data breaches: Remote work surge led to more data breaches. Proxyrack found healthcare breaches costing $9.23 million and the finance sector averaging $5.27 million.
- Targeted attacks: The U.S. faces 7,221,177 incidents per million people, the highest globally. The average breach cost for U.S. companies is $9,050,000.
- More than just financial loss: Data breaches inflict enduring financial and reputational harm, eroding customer trust. To preserve brand integrity and loyalty, companies must prioritize cybersecurity.
- The human element: Remote employees are vulnerable to cyberattacks due to personal devices and unsecured networks. Mistakes like phishing or weak passwords risk breaches.
- The need for proactive defense: Businesses need a proactive approach to tackle remote data breaches: train employees, use secure clouds, and update technology and systems.
Advantages of Remote Network Security
Securing your remote networks offers significant advantages to businesses, particularly in an era marked by escalating cyber crimes and the rise of remote work. Let’s explore the four main benefits of implementing robust security measures.
Secure Your Network Everywhere, on Any Device
Remote network security protects data and systems, blocking unauthorized access from the company or personal devices.
Improved Endpoint Protection
Vulnerable endpoints, such as laptops and smartphones, attract cybercriminals. Maintaining the security of your networks ensures all endpoints remain protected. We use VPNs, multi-factor authentication, and security tools to reinforce endpoint safety.
Secure Web Access for All Employees
Employees frequently access online company resources. This security encrypts online interactions, granting access only to authorized users.
Raise Awareness of Security Issues
Empowering employees with remote security fosters cyber awareness. Training, updates, and drills cultivate a vigilant defense against threats.
18 Tips to Improve Your Remote Network Security
The digital shift has propelled many businesses towards a remote work model. With this evolution comes a heightened need to prioritize the security of your remote networks.
Here are 18 strategies to bolster your defenses:
Protect Endpoints for All Remote Users
Secure all devices connecting to the network to reduce breach risks.
Reduce Attack Surface in Remote Work
Frequently update and patch software. Also, practice access limitation.
Use Multi-Factor Authentication
Strengthen security by mandating multiple identification forms before granting access.
Use Password Managers
Urge employees to adopt password managers.
Implement Single Sign-on Technology
Streamline login: utilize a single set of credentials for multiple applications.
Use VPNs
By encrypting internet traffic, Virtual Private Networks ensure confidential data transmission.
Adjust Logs and Security Information Tracking
Consistently revise and refresh logs to pinpoint and address anomalous or unauthorized actions.
Educate Your Employees and Contractors
Equip everyone with knowledge on contemporary cybersecurity threats and best practices to foster an informed, watchful team.
Create Clear Remote Work Policies
Craft clear-cut rules guiding employees’ interaction with company resources during remote work.
Build Intrusion Prevention and Detection Systems
Set up systems to check the network for malevolent activities. This ensures you’re using preventive measures against detected threats.
Use Firewalls
Position firewalls as protective barriers, scrutinizing incoming and outgoing traffic to safeguard against potential risks.
Encrypt and Back-up Data
Prioritize encryption of sensitive data and consistently back up crucial information to avert data loss.
Use Secure Software
Opt for reputable software that aligns with the organizational security benchmarks.
Implement an Identity Access and Management (Iam) Framework
With IAM, manage user identities and their access rights, ensuring that only vetted individuals can tap into particular resources.
Build Service-Level Agreements With Third-Party Vendors
Hold third-party associates to the same security standards as your company.
Ensure Mobile Security
Prioritize mobile device security as usage rises, safeguarding organizational data access.
Implement Direct Application Access Processes
Let users directly access applications without jeopardizing the security of the primary network.
Secure Specific Remote Work Devices
Ensuring the security of devices designated for remote work goes beyond the hardware; it’s about integrating sound policies, technologies, and procedures.
Here’s a concise breakdown:
- Criteria: Establish straightforward criteria for determining which employees are eligible for remote access.
- Technologies & features: Opt for secure technologies offering valuable features like encryption.
- IT resource access: Deploy specific IT assets.
- Network resources: Guarantees a secure connection.
- IT personnel: Assign dedicated staff.
- Emergency protocols: Have a quick response strategy for emergencies like security breaches.
- Integration: Integrate remote access security with other data protection measures.
Technologies Used for Business Remote Network Security
In the evolving landscape of remote work, businesses leverage advanced technologies to fortify their network security. These technologies protect sensitive data and ensure seamless operations across distributed teams.
Here’s a closer look at some of the pivotal technologies in use:
Endpoint Security
Endpoint security safeguards all user devices in a network, which is crucial for remote work and personal device use. It defends against cyber threats, ensuring data integrity.
Virtual Private Networks (VPN)
Business VPNs safeguard data between user devices and the company’s network, which is vital for remote workers accessing company resources securely.
Zero Trust Network Access (ZTNA)
ZTNA: “Never trust, always verify” principle replaces perimeters. Every user and device is verified for network access. It’s not a VPN alternative, the two work hand in hand to secure your assets.
Network Access Control
The technology assesses and enforces network access policies based on device health, update status, and more for compliance.
Single Sign-on
SSO simplifies login across apps, enhances convenience, saves time, and reduces password-related breaches.
Secure Access Service Edge (SASE)
SASE: Cloud-based service combining network and security functions for modern businesses.
The Future of Business Security in a Remote World
The digital age demands remote network security for businesses. Global events shift to remote work and expose traditional vulnerabilities. This article provides insights and actionable tips on securing your networks to bolster your business operations.
With evolving technology come evolving threats. To keep your business secure and efficient, stay informed, proactive, and adaptable to emerging challenges. By adopting these tools and strategies, you’ll confidently navigate the future of remote work securely.
Looking for a secure and seamless digital future for your business? Click here to book a consultation and enjoy strengthened security, tailor-made remote work solutions, and a robust digital infrastructure.
Source :
https://www.perimeter81.com/blog/network/business-remote-network-security








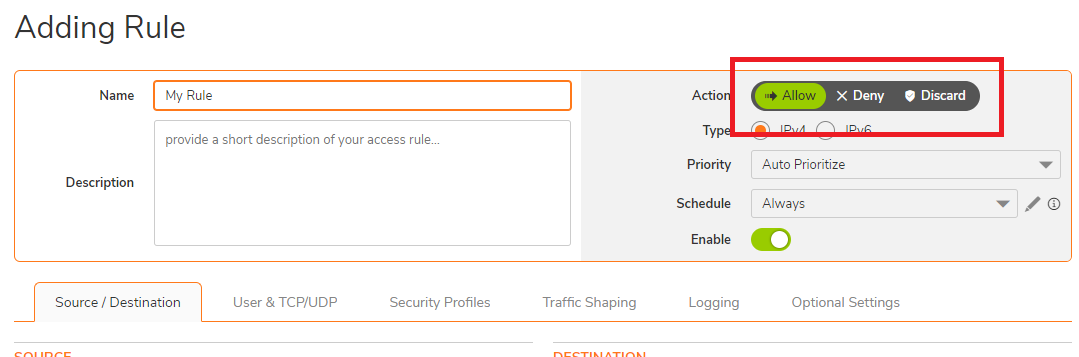
 NOTE: When creating a new access rule, the default Action on your firewall is set to Allow.
NOTE: When creating a new access rule, the default Action on your firewall is set to Allow.