Let’s do a show of hands — who loves jargon? Anyone?
I didn’t think so.
Face it, aside from trivia champions, jargon doesn’t make life any easier for us. If you’re attending your first security conference this year, you might feel like you need an interpreter to make sense of the technical terminology and acronyms you’ll find around every corner.
At Cisco Umbrella, we’re fluent in cybersecurity – and we want to help you make sense of the often-confusing security landscape! In this post, we define key cybersecurity terms that everyone should know in 2020 — and beyond.
Part 1: Threats
Backdoor: A backdoor is an access point designed to allow quick and undetected entrance to a program or system, usually for malicious purposes. A backdoor can be installed by an attacker using a known security vulnerability, and then used later to gain unfettered access to a system.
Botnet: A botnet is a portmanteau for “robot network.” It’s a collection of infected machines that can be used for any number of questionable activities, from cryptomining to DDoS attacks to automated spam comments on blogs.
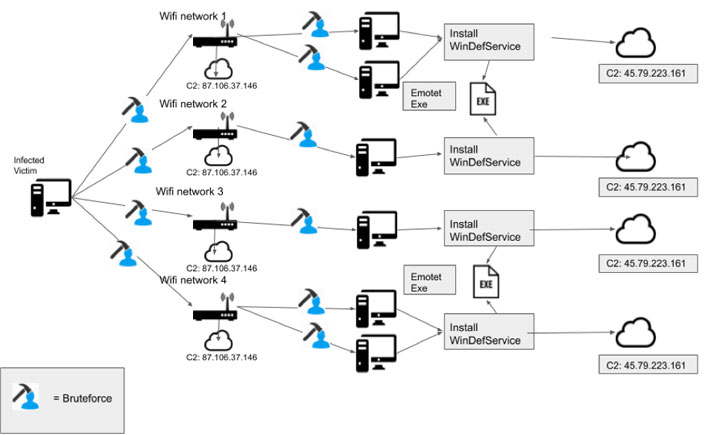
Command-and-control (C2) attacks: Command-and-control attacks are especially dangerous because they are launched from inside your network. Security technologies like firewalls are designed to recognize and stop malicious activity or files from entering your network. However, a command-and-control attack is trickier than a standard threat. A file doesn’t start out showing any malicious behavior, so it is deemed harmless by your firewall and permitted to enter your network. Once inside, the file stays dormant for a set period of time or after being triggered remotely. Then, the file reaches out to a malicious domain and downloads harmful data, infecting your network.
Denial of Service (DoS) Attack: This type of attack consumes all of the resources of a target so that it can no longer be used or reached, effectively taking it down. DoS attacks are designed to take a website or server offline, whether for monetary, political, or other reasons. A DDoS, or Distributed Denial of Service attack, is a subcategory of DoS attack that is carried out using two or more hosts, often via a botnet.
Drive-by download: A drive-by download installs malware invisibly in the background when the user visits a malicious webpage, without the user’s knowledge or consent. Often, drive-by downloads take advantage of browser or browser plug-in vulnerabilities that accept a download under the assumption that it’s a benign activity. Using an up-to-date secure browser can help protect you against this type of attack.
Exploit: An exploit is any attack that takes advantage of a weakness in your system. It can make use of software, bits of data, and even social engineering (like pretending to be someone from your IT team who needs your password to perform a security update). To minimize exploits, it’s important to keep your software up-to-date and to be aware of social engineering techniques (see below).
Malware: Malware is a generic term for any program installed on a system with the intent to corrupt, damage, or disable that system. Razy, TeslaCry, NotPetya, and Emotet are a few recent examples.
- Cryptomining malware: Cryptomining by itself is not necessarily malicious — many people mine crypto currency on their own systems. Malicious cryptomining, however, is a browser- or software-based threat that enables bad actors to hijack system resources to generate crypto currencies. Cryptomining malware is an easy way for bad actors to generate cash while remaining anonymous and without having to use their own resources. Learn more about the cryptomining malware threat.
- Ransomware: Ransomware is malware used to encrypt a victim’s data with an encryption key that is known only to the attacker. The data becomes unusable until the victim pays a ransom to decrypt the data (usually in cryptocurrency). Ransomware is a fast-growing and serious threat — learn more in our newly updated guide to ransomware defense.
- Rootkits: A rootkit is a malicious piece of code that hides itself in your system, prevents detection, and enables bad actors to gain continued access to your system. If attackers gain full access to your system once, they can use rootkits to continue that access over a long period of time.
- Spyware: Malicious code that gathers information about you and your browsing habits, and then sends that information to a third party.
- Trojans: A trojan is a seemingly innocuous program that acts as a front for malicious code hiding inside. Trojans can do any number of things, from stealing data to allowing remote system control. These programs take their name from the famous Grecian “Trojan Horse” that took advantage of a similar vulnerability.
- Viruses: Often used as a blanket term, a virus is a piece of code that attaches itself to files, such as email attachments or files you download online. Once it infects your system, it can cause all kinds of problems, whether that means deleting system files or corrupting your data. Computer viruses also replicate and spread across networks – just like viruses in the physical world.
- Worms: A worm is a type of malware that clones itself in order to spread to other computers, performing various damaging actions on whatever system it infects. Unlike a virus, a worm exists as a standalone entity — it isn’t hidden inside something else like an attachment.
MitM or Man-in-the-Middle Attack: A MitM attack is pretty much what it sounds like. An attacker will intercept, relay, and potentially change messages between two parties without their knowledge. MitM can be used to break encryption, compromise account details, or gain access to systems by impersonating a user.
Phishing: Phishing is a technique that mimics a legitimate communication (like an email from your online bank) to steal sensitive information. Like fishermen with a lure, attackers will attempt to take your personal information by using fake emails, forms, and web pages to coax you to provide it to them.
- Spear phishing is a form of phishing that targets one specific individual by using publicly accessible data about them, like from a business card or social media profile.
- Whale phishing goes one step further than spear phishing and describes a targeted attack on a high-ranking individual, like a CEO or government official.
Social engineering: A general term for any activity in which an attacker is trying to manipulate you into revealing information, whether over email, phone, web forms, or social media platforms. Passwords, account credentials, social security numbers — we often don’t think twice about giving this information away to someone we can trust, but who’s really on the other end of the line? Protect yourself, and think twice before sharing. It’s always OK to verify the request for information in another way, like calling an official customer support number.
Zero-day (0day): A zero day attack is when a bad actor exploits a new, previously unknown software vulnerability for which there is no patch. It’s a constant struggle to stay ahead of attackers, but you don’t have to do it alone — you can get help from the security experts at Cisco Talos.
Part 2: Solutions
Anti-malware: Anti-malware software is a broad category of software designed to block, root out, and destroy viruses, worms, and other nasty things that are described in this list. These products need to be updated regularly to ensure that they remain effective against new threats. They can be deployed at various points in the network chain (email, endpoint, data center, cloud) and either on-premises or delivered from the cloud.
Cloud access security broker (CASB): This is software that provides the ability to detect and report on the cloud applications that are in use across your environment. It provides visibility into cloud apps in use as well as their risk profiles, and the ability to block/allow specific apps. Read more about securing cloud apps here.
Cloud security: this is a subcategory of information security and network security. It is a broad term that can include security policies, technologies, applications, and controls that are used to protect sensitive company and user data wherever it is exposed in a public, private, or hybrid cloud environment.
DNS-layer security: This is the first line of defense against threats because DNS resolution is the first step in establishing a connection to the internet. It blocks requests to malicious and unwanted destinations before a connection is even established — stopping threats over any port or protocol before they reach your network or endpoints. Learn more about DNS-layer security here.
Email security: This refers to the technologies, policies, and practices used to secure the access and content of email messages within an organization. Many attacks are launched via email messages, whether through targeted attacks (see note on phishing above) or malicious attachments or links. A robust email security solution protects you from attacks whether email is in transit across your network or when it is on a user’s device.
Encryption: This is the process of scrambling messages so that they cannot be read until they are decrypted by the intended recipient. There are several types of encryption, and it’s an important component of a robust security strategy.
Endpoint security: if DNS-layer security is the first line of defense against threats, then you might think of endpoint security as the last line of defense! Endpoints can include desktop computers, laptop computers, tablets, mobile phones, desk phones, and even wearable devices — anything with a network address is a potential attack path. Endpoint security software can be deployed on an endpoint to protect against file-based, fileless, and other types of malware with threat detection, prevention, and remediation capabilities.
Firewall: Imagine all the nasty, malicious stuff on the Internet without anything to stop it. A firewall stands between your trusted entities and whatever lies beyond, controlling access based on security rules. A firewall can be hardware or software, a standalone security appliance or a cloud-delivered solution.
Next-generation firewall (NGFW): This is the industry’s new solution for an evolved firewall. It is typically fully integrated with the rest of the security stack, threat-focused, and delivers comprehensive, unified policy management of firewall functions, application control, threat prevention, and advanced malware protection from the network to the endpoint.
Security information and event management (SIEM): This is a broad term for products that deal with security information management (SIM) and security event management (SEM). These systems allow for aggregation of information and events into a single “pane of glass” for security teams to use.
Secure web gateway (SWG): This is a proxy that can log and inspect all of your web traffic for greater transparency, control, and protection. It allows for real-time inspection of inbound files for malware, sandboxing, full or selective SSL decryption, content filtering, and the ability to block specific user activities in select apps.
Secure internet gateway (SIG): This is a cloud-delivered solution that unifies a variety of connectivity, content control, and access technologies to provide users with safe access to the internet, both on and off the network. By operating from the cloud, a SIG protects user access anywhere and everywhere, with traffic routing to the gateway for inspection and policy enforcement regardless of what users are connecting to, or where they’re connecting from. Because a SIG extends security beyond the edge of the traditional network — and without the need for additional hardware or software — thousands of enterprises have adopted it as a modern catch-all for ensuring that users, devices, endpoints, and data have robust protection from threats.
Secure access service edge (SASE): Gartner introduced an entirely new enterprise networking and security category called “secure access service edge.” SASE brings together networking and security services into one unified solution designed to deliver strong security from edge to edge — in the data center, at remote offices, with roaming users, and beyond. By consolidating a variety of powerful point solutions into one solution that can be deployed anywhere from the cloud, SASE can provide better protection and faster network performance, while reducing the cost and work it takes to secure the network.
Cybersecurity is always evolving, and it can be hard to keep up with the rapid pace of changes. Be sure to bookmark this blog post – we’ll keep it up to date as new threats and technologies emerge. To learn more, check out our recent blog posts about cybersecurity research, or come chat with our security experts in person in Barcelona at Cisco Live EMEA this month. Don’t be shy!
Source :
https://umbrella.cisco.com/blog/2020/01/14/cybersecurity-terms-and-threats-you-need-to-know-in-2020/