Researchers have disclosed a security shortcoming affecting three different WordPress plugins that impact over 84,000 websites and could be abused by a malicious actor to take over vulnerable sites.
“This flaw made it possible for an attacker to update arbitrary site options on a vulnerable site, provided they could trick a site’s administrator into performing an action, such as clicking on a link,” WordPress security company Wordfence said in a report published last week.
Tracked as CVE-2022-0215, the cross-site request forgery (CSRF) flaw is rated 8.8 on the CVSS scale and impacts three plugins maintained by Xootix —
- Login/Signup Popup (Inline Form + Woocommerce),
- Side Cart Woocommerce (Ajax), and
- Waitlist Woocommerce (Back in stock notifier)
Cross-site request forgery, also known as one-click attack or session riding, occurs when an authenticated end-user is tricked by an attacker into submitting a specially crafted web request. “If the victim is an administrative account, CSRF can compromise the entire web application,” OWASP notes in its documentation.
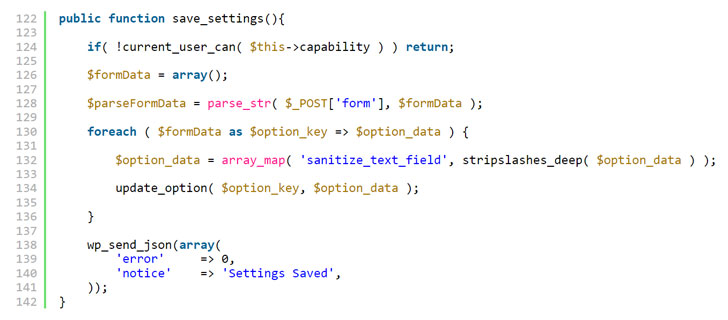
Specifically, the vulnerability has its origin in a lack of validation when processing AJAX requests, effectively enabling an attacker to update the “users_can_register” (i.e., anyone can register) option on a site to true and set the “default_role” setting (i.e., the default role of users who register at the blog) to administrator, granting complete control.
Login/Signup Popup is installed on over 20,000 sites, while Side Cart Woocommerce and Waitlist Woocommerce have been installed on more than 4,000 and 60,000 sites, respectively.
Following responsible disclosure by Wordfence researchers in November 2021, the issue has been addressed in Login/Signup Popup version 2.3, Side Cart Woocommerce version 2.1, and Waitlist Woocommerce version 2.5.2.
The findings come a little over a month after attackers exploited weaknesses in four plugins and 15 Epsilon Framework themes to target 1.6 million WordPress sites as part of a large-scale attack campaign originating from 16,000 IP addresses.
“Though this Cross-Site Request Forgery (CSRF) vulnerability is less likely to be exploited due to the fact that it requires administrator interaction, it can have a significant impact to a successfully exploited site and, as such, it serves as an incredibly important reminder to remain aware when clicking on links or attachments and to ensure that you are regularly keeping your plugins and themes up to date,” Wordfence’s Chloe Chamberland said.
Source :
https://thehackernews.com/2022/01/high-severity-vulnerability-in-3.html