brandon.lee 02 June 2023
The process to install Windows Updates can be a pain. Managing WSUS servers can be a headache too. However, with PowerShell, a special module, and some automation, we can schedule and automate the installation process of Windows Updates. Let’s look at PSWindowsupdate automated Windows Updates with PowerShell and see how it can come to the rescue for keeping your Windows environment up-to-date.
Table of contents
- What is PSWindowsUpdate?
- Why is Installing Windows Updates Important?
- Installing the PSWindowsUpdate Module
- Importing the PSWindowsUpdate Module
- Checking for Available Updates
- Downloading Windows Updates
- Installing Windows Updates
- Managing Windows Update History
- Customizing Update Installation with an XML File
- Scheduling Updates with Task Scheduler
- Installing Specific Updates
- Installing Only Security Updates
- Hiding Specific Updates
- Checking if a Reboot is Required
- Automate Windows Updates using PSWindowsUpdate
- PSWindowsupdate Frequently Asked Questions
- Using Automation in the home lab
- Wrapping up
- Other posts you may like
What is PSWindowsUpdate?
PSWindowsUpdate is a PowerShell third-party module found in the PowerShell gallery repository available for download designed to help administrators manage Windows updates and install updates flexibly and precisely.
Unlike the standard Windows Update Service Manager (WSUS) interface, the PSWindowsUpdate module provides commands for downloading, installing, and managing updates in an automated way. However, it can work in conjunction with WSUS or pull updates directly from Microsoft.
Admins can control every aspect of Windows updates with this module – from viewing available updates and initiating installations to setting update schedules. It includes advanced features like installing specific updates, managing hidden updates, or even automating the entire update process using the Windows Task Scheduler.
Why is Installing Windows Updates Important?
Before diving into the PSWindowsupdate module, why is installing Windows updates important? Installing Windows updates is essential to maintaining a secure and stable system. These updates often contain security patches that protect your systems from vulnerabilities and threats. By regularly installing these updates, you’re ensuring your system’s defenses are up-to-date.
Updates also introduce new features, improve system stability, and fix existing system and software bugs. This can lead to better performance, fewer errors, and a smoother overall user experience. As such, regular updates can go a long way in minimizing downtime and reducing the need for troubleshooting.
If you are a system administrator, it may seem like a headache to patch systems constantly. However, you will thank yourself later for having a fully patched system when the next ransomware variant takes advantage of known patched vulnerabilities. Also, if you are looking at introducing any new integration or software into the environment, it is always best practice to be on the latest version of Windows, patches installed, etc.
Installing the PSWindowsUpdate Module
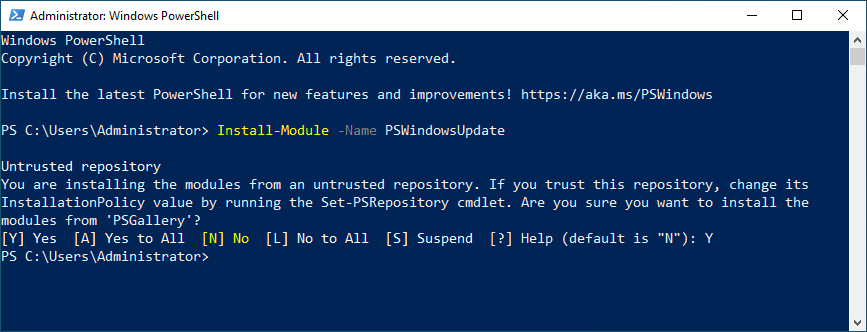
The installation process for the PSWindowsUpdate module starts with the command line in your PowerShell console. You need to install the module from the PowerShell gallery by typing:
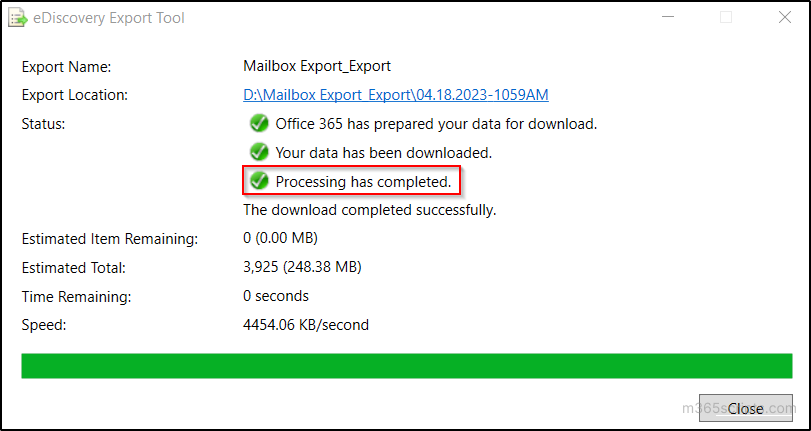
Install-Module -Name PSWindowsUpdateThis command will download and install the module on your local system. However, it’s critical to note that you may need administrator privileges to install modules. Open the PowerShell prompt as an admin and run the command.
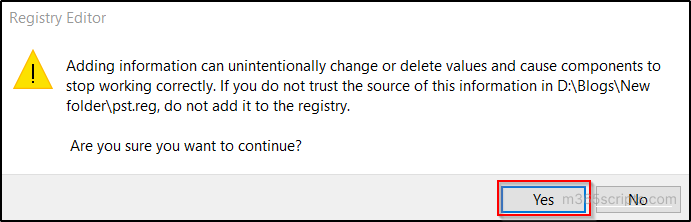
You will be prompted to trust the untrusted repository, which is normal.
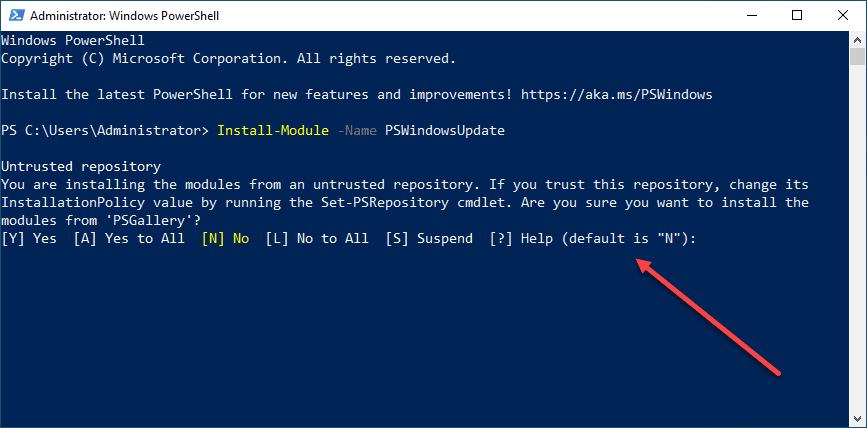
Type “Y” to trust the PSGallery repository.
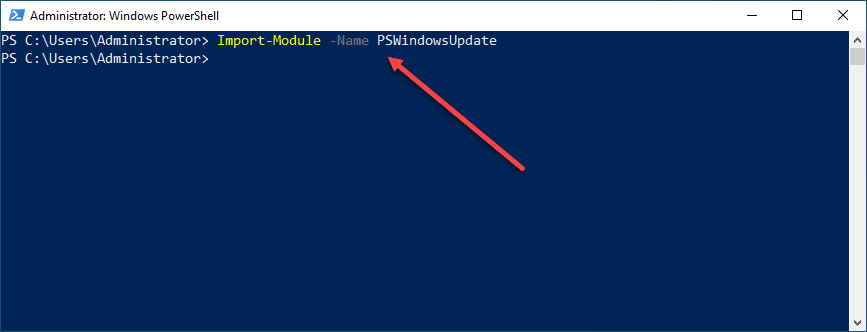
Importing the PSWindowsUpdate Module
Once installed, you need to import the module PSWindowsUpdate to begin using it. Use the following command:
Import-Module -Name PSWindowsUpdateIt loads the module into your active PowerShell session, making the related cmdlets available for use.
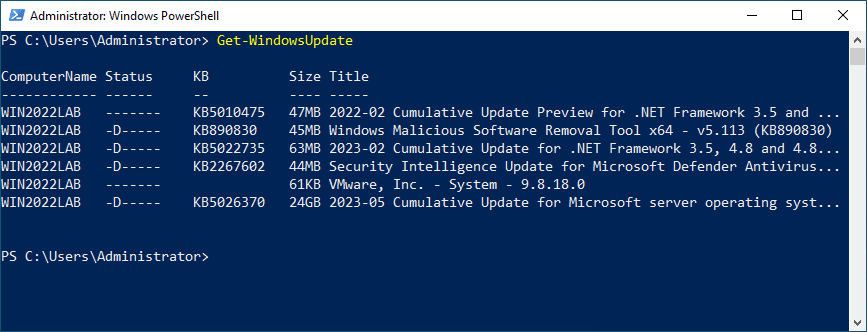
Checking for Available Updates
Upon successful import of the PSWindowsUpdate module, you can quickly check for available updates using the command:
Get-WindowsUpdateThis command will query your machine’s Windows Update Client settings and connect to the Microsoft Update servers to fetch the list of all available updates. You can see critical updates, security updates, and all other types of updates that your system can download and install.
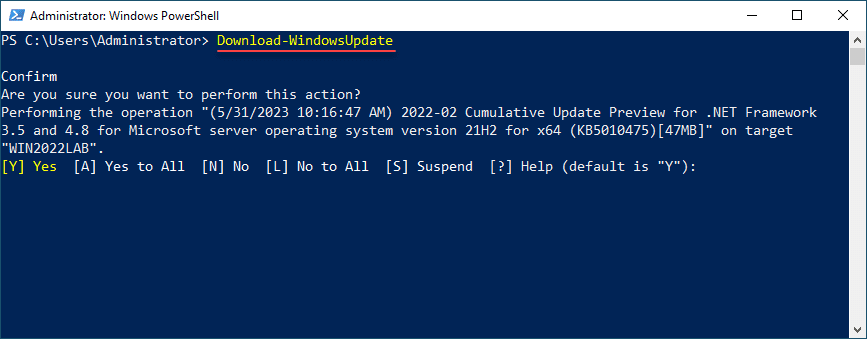
Downloading Windows Updates
The PSWindowsUpdate module offers the command:
Download-WindowsUpdateUse this to download Windows updates. Depending on your settings, this command initiates the download process for all approved updates from the Windows Server Update Service (WSUS) or Microsoft Update.
Installing Windows Updates
With the updates downloaded, you can install them using the ‘Install-WindowsUpdate‘ command. This command installs all downloaded updates, following which your system might need to reboot.
Install-WindowsUpdate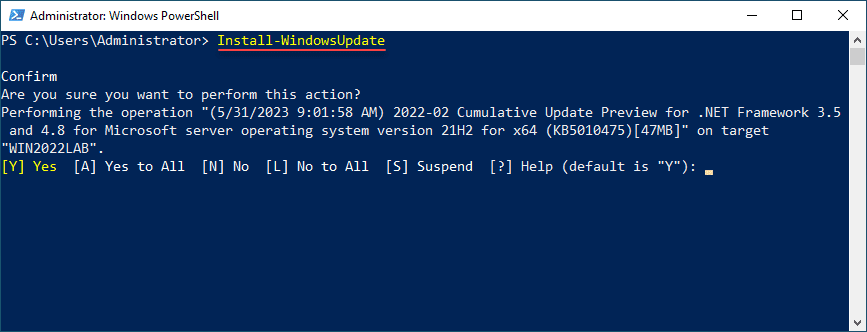
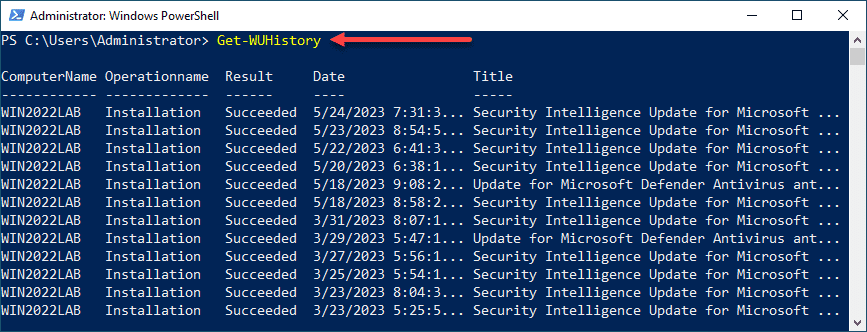
Managing Windows Update History
The PSWindowsUpdate module provides an opportunity to access your system’s update history. You can use the ‘Get-WUHistory‘ command to get a detailed log of all installed updates.
Get-WUHistoryThis command returns a detailed list, including the KB number, update title, and the status of the installed updates.
Customizing Update Installation with an XML File
Advanced users might appreciate the ability to customize update installations using XML files. These files can specify category names to include or exclude from the update process. You can also use them to specify whether to include or exclude updates marked for automatic installation.
Scheduling Updates with Task Scheduler
In many environments, you may want to run the PSWindowsupdate command in an automated way. One way you can do this is by leveraging the power of the Windows Task Scheduler in conjunction with the PSWindowsUpdate module.
Using this combination, you can automate the download and install process at specific intervals, ensuring your system stays updated without manual intervention. We will take a look below at a script you can schedule with the Task Manager to run on a regular interval.
Installing Specific Updates
You can install specific updates using their unique KB number with the Install-WindowsUpdate command. For example, suppose you only want to install the update with the KB number KB4012606, you can do so with the following command:
Install-WindowsUpdate -KBArticleID KB4012606 -AcceptAll -AutoRebootThis command will only install the specified update and perform an automatic reboot if necessary.
Installing Only Security Updates
If you wish only to install security updates, you can do so with the following command:
Get-WindowsUpdate -Category 'SecurityUpdates' | Install-WindowsUpdateThis command first fetches only the security updates and then pipes them into the Install-WindowsUpdate command, installing only the security updates.
Hiding Specific Updates
There may be times when you want to hide a problematic update. If you want to hide Windows updates, maybe because it’s causing issues on your system, you can do so with the Hide-WindowsUpdate command. Suppose you want to hide the update with the KB number KB4012606, you can do so with the following command:
Hide-WindowsUpdate -KBArticleID KB4012606This command will hide the specified update, preventing it from appearing in future searches for updates.
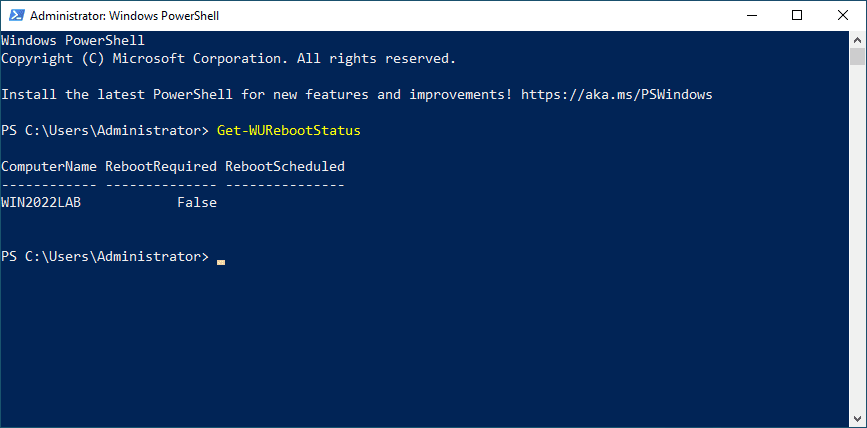
Checking if a Reboot is Required
You may want to see if there is a pending reboot required. If you want to check if a reboot is required after installing updates, you can do so with the Get-WURebootStatus command like so:
Get-WURebootStatusThis command will check and let you know if any installed updates require a reboot.
In the example, replace the placeholder KB numbers in the commands with the actual KB number of the update you’re interested in. Also, always ensure to run these commands in a safe and controlled environment, particularly when executing them on production systems or remote computers.
Automate Windows Updates using PSWindowsUpdate
Automation is one of the powerful features of PowerShell and by extension, the PSWindowsUpdate module. In this section, we’ll cover an example of how to write a script for automating Windows updates using PSWindowsUpdate.
# Import the PSWindowsUpdate module
Import-Module PSWindowsUpdate
# Get all available updates
$updates = Get-WindowsUpdate -MicrosoftUpdate
# Filter out optional updates
$importantUpdates = $updates | Where-Object {$_.IsDownloaded -eq $true -and $_.IsMandatory -eq $true}
# Install important updates
$importantUpdates | Install-WindowsUpdate -AcceptAll -AutoReboot
In this script, we first import the PSWindowsUpdate module. We then fetch all available updates using Get-WindowsUpdate. Using Where-Object, we filter out only the important (mandatory and already downloaded) updates, ignoring the optional ones. Lastly, we install these important updates using Install-WindowsUpdate, automatically accepting EULAs and rebooting if necessary.
You can automate the execution of this script using Task Scheduler. Here’s a basic example of how you can do this:
- Open Task Scheduler and create a new task.
- In the Triggers tab, set the schedule for the task according to your needs (for example, daily at 3 AM).
- In the Actions tab, select ‘Start a program’ and input powershell.exe as the program.
- In the ‘Add arguments’ field, input -ExecutionPolicy Bypass -File “c:your script file path.ps1” where <your script file path> is the path to your PowerShell script.
- Finish the wizard and the task will be scheduled.
Remember to replace the path to the script with the actual path of your script file. The system will automatically execute the update script at the specified time.
This script and scheduling are basic examples. You may need to modify the script and task parameters according to your specific requirements, such as filtering updates based on criteria or sending a report by email after installation.
Also, be sure to test these scripts in a safe and controlled environment before deploying them in production, especially when executing them on remote computers.
PSWindowsupdate Frequently Asked Questions
Can I use the PSWindowsUpdate module to manage updates on remote computers?
Using the PSWindowsUpdate module, you can manage updates both locally and on remote computers. You must ensure you have all the necessary permissions as you would normally to administer and manage a remote machine.
Can I automate the update process using the PSWindowsUpdate module?
One of the strong suits of the PSWindowsUpdate module is the ability you have to automate the process of applying Windows Updates. You can easily create a simple PowerShell script to download and install Windows Updates. It can also apply various logic such as hiding updates, downloading only certain types of updates, etc. Using Task Scheduler, it is easy to have a way to trigger the automation of PSWindowsUpdate.
How do I view hidden updates using PSWindowsUpdate?
You can use the Get-WUHiddenUpdate command to view all hidden updates on your system. If you wish to unhide an update, use the UnHide-WindowsUpdate command with the appropriate KB number.
How can I install specific categories of updates using the PSWindowsUpdate module?
You can filter updates based on a particular category using PSWindowsUpdate. It is common to see administrators only install the “security updates” available for an operating system. You can easily accomplish this with the following command:
Get-WindowsUpdate -Category 'SecurityUpdates' | Install-WindowsUpdate.Wrapping up
The PSWindowsUpdate module is a great way for system administrators to manage single or multiple Windows servers using a fully automated solution built on top of PowerShell. It provides many capabilities that give you full control over the Windows Update service. You can use it to review available updates, download approved updates, or manage the update history. The PSWindowsupdate PowerShell module can help streamline your system’s update process, including all Windows PCs and Servers across the board.
Other posts you may like
- Automated Patching of Microsoft Wormable RDP Vulnerabilities
- Five simple tweaks for Windows 7
- Untangle 11.0 new features and changes
- Easy ways to get to Windows Task Manager
- Updating vCenter Server 5.5 to update 2
Source :
https://www.virtualizationhowto.com/2023/06/pswindowsupdate-automated-windows-updates-with-powershell/

 Fun fact: In my environment that change made the deletions go 30 times faster!!!
Fun fact: In my environment that change made the deletions go 30 times faster!!!