These statistics are based on detection verdicts of Kaspersky products received from users who consented to providing statistical data.
Quarterly figures
According to Kaspersky Security Network, in Q2 2022:
- 5,520,908 mobile malware, adware and riskware attacks were blocked.
- The most common threat to mobile devices was adware: 25.28% of all threats detected.
- 405,684 malicious installation packages were detected, of which:
- 55,614 packages were related to mobile banking Trojans;
- 3,821 packages were mobile ransomware Trojans.
Quarterly highlights
In the second quarter of 2022, cybercriminal activity continued to decline — if the number of attacks on mobile devices is any indication.
https://e.infogram.com/_/kUJZ2IuFyVL5rs1NUqoG?parent_url=https%3A%2F%2Fsecurelist.com%2Fit-threat-evolution-in-q2-2022-mobile-statistics%2F107123%2F&src=embed#async_embed
Number of attacks targeting users of Kaspersky mobile solutions, Q1 2020 — Q2 2022 (download)
As in the previous quarter, fraudulent apps occupied seven out of twenty leading positions in the malware rankings. That said, the total number of attacks by these apps started to decrease.
Interestingly enough, some fraudulent app creators were targeting users from several countries at once. For instance, J-Lightning Application purported to help users to invest into a Polish oil refinery, a Russian energy company, a Chinese cryptocurrency exchange and an American investment fund.
On the contrary, the number of attacks by the RiskTool.AndroidOS.SpyLoan riskware family (loan apps that request access to users’ text messages, contact list and photos) more than quadrupled from the first quarter. The majority of users whose devices were found to be infected with this riskware were based in Mexico: a third of the total number of those attacked. This was followed by India and Colombia. The ten most-affected countries include Kenya, Brazil, Peru, Pakistan, Nigeria, Uganda and the Philippines.
The second quarter was also noteworthy for Europol taking down the infrastructure of the FluBot mobile botnet, also known as Polph and Cabassous. This aggressively spreading banking Trojan attacked mainly users in Europe and Australia.
Mobile threat statistics
In Q2 2022, Kaspersky detected 405,684 malicious installation packages, a reduction of 110,933 from the previous quarter and a year-on-year decline of 480,421.
https://e.infogram.com/_/sggcRCeC8v5IMtDdh0MY?parent_url=https%3A%2F%2Fsecurelist.com%2Fit-threat-evolution-in-q2-2022-mobile-statistics%2F107123%2F&src=embed#async_embed
Number of detected malicious installation packages, Q2 2021 — Q2 2022 (download)
Distribution of detected mobile malware by type
https://e.infogram.com/_/xd4vJYpEUtvNfzYvS1xv?parent_url=https%3A%2F%2Fsecurelist.com%2Fit-threat-evolution-in-q2-2022-mobile-statistics%2F107123%2F&src=embed#async_embed
Distribution of newly detected mobile malware by type, Q1 and Q2 2022 (download)
Adware ranked first among all threats detected in Q2 2022 with 25.28%, exceeding the previous quarter’s figure by 8.36 percentage points. A third of all detected threats of that class were objects of the AdWare.AndroidOS.Ewind family (33.21%). This was followed by the AdWare.AndroidOS.Adlo (22.54%) and AdWare.AndroidOS.HiddenAd (8.88%) families.
The previous leader, the RiskTool riskware, moved to second place with 20.81% of all detected threats, a decline of 27.94 p.p. from the previous quarter. More than half (60.16%) of the discovered apps of that type belonged to the Robtes family.
Various Trojans came close behind with 20.49%, a rise of 5.81 p.p. on the previous quarter. The largest contribution was made by objects belonging to the Mobtes (38.75%), Boogr (21.12%) and Agent (18.98%) families.
Top 20 mobile malware programs
Note that the malware rankings below exclude riskware or PUAs, such as RiskTool or adware.
| Verdict | %* | |
| 1 | DangerousObject.Multi.Generic | 21.90 |
| 2 | Trojan-SMS.AndroidOS.Fakeapp.d | 10.71 |
| 3 | Trojan.AndroidOS.Generic | 10.55 |
| 4 | Trojan.AndroidOS.GriftHorse.ah | 6.07 |
| 5 | Trojan-Spy.AndroidOS.Agent.aas | 5.40 |
| 6 | Trojan.AndroidOS.GriftHorse.l | 3.43 |
| 7 | DangerousObject.AndroidOS.GenericML | 3.21 |
| 8 | Trojan-Dropper.AndroidOS.Agent.sl | 2.82 |
| 9 | Trojan.AndroidOS.Fakemoney.d | 2.33 |
| 10 | Trojan.AndroidOS.Fakeapp.ed | 1.82 |
| 11 | Trojan.AndroidOS.Fakeapp.dw | 1.68 |
| 12 | Trojan.AndroidOS.Fakemoney.i | 1.62 |
| 13 | Trojan.AndroidOS.Soceng.f | 1.59 |
| 14 | Trojan-Ransom.AndroidOS.Pigetrl.a | 1.59 |
| 15 | Trojan.AndroidOS.Boogr.gsh | 1.56 |
| 16 | Trojan-Downloader.AndroidOS.Necro.d | 1.56 |
| 17 | Trojan-SMS.AndroidOS.Agent.ado | 1.54 |
| 18 | Trojan-Dropper.AndroidOS.Hqwar.gen | 1.54 |
| 19 | Trojan.AndroidOS.Fakemoney.n | 1.52 |
| 20 | Trojan-Downloader.AndroidOS.Agent.kx | 1.45 |
* Unique users attacked by this malware as a percentage of all attacked users of Kaspersky mobile solutions.
First and third places went to DangerousObject.Multi.Generic (21.90%) and Trojan.AndroidOS.Generic (10.55%), respectively, which are verdicts we use for malware detected with cloud technology. Cloud technology is triggered whenever the antivirus databases lack data for detecting a piece of malware, but the antivirus company’s cloud already contains information about the object. This is essentially how the latest malware types are detected.
Trojan-SMS.AndroidOS.Fakeapp.d rose from third to second place with 10.71%. This malware is capable of sending text messages and calling predefined numbers, displaying ads and hiding its icon.
Members of the Trojan.AndroidOS.GriftHorse family took fourth and sixth places with 6.07% and 3.43%, respectively. This family includes fraudulent apps that purchase paid subscriptions on the user’s behalf.
Trojan-Spy.AndroidOS.Agent.aas (5.40%), an evil twin of WhatsApp with a spy module built in, retained fifth position.
The verdict of DangerousObject.AndroidOS.GenericML (3.21%) came seventh. These verdicts are assigned to files recognized as malicious by our machine-learning systems.
Trojan-Dropper.AndroidOS.Agent.sl (2.82%), a dropper that unpacks and runs a banking Trojan on devices, remained in eighth place. Most of the attacked users were based in Russia or Germany.
Trojan.AndroidOS.Fakemoney.d slid from second to ninth place with 2.33%. Other members of the family occupied twelfth and nineteenth places in the rankings. These are fraudulent apps that offer users to fill out fake welfare applications.
Trojan.AndroidOS.Fakeapp.ed dropped to tenth place from sixth with 1.82%; this verdict covers fraudulent apps purporting to help with investing in gas utilities and mostly targeting Russian users.
Trojan.AndroidOS.Fakeapp.dw dropped from tenth place to eleventh with 1.68%. This verdict is assigned to various scammer apps, for example, those offering to make extra income.
Trojan.AndroidOS.Soceng.f (1.59%) dropped from twelfth to thirteenth place. This Trojan sends text messages to people in your contacts list, deletes files on the user’s SD card, and overlays the interfaces of popular apps with its own window.
Trojan-Ransom.AndroidOS.Pigetrl.a dropped from eleventh to fourteenth place with 1.59%. This malware locks the screen, asking to enter an unlock code. The Trojan provides no instructions on how to obtain this code, which is embedded in the body of the malware.
The verdict of Trojan.AndroidOS.Boogr.gsh occupied fifteenth place with 1.56%. Like DangerousObject.AndroidOS.GenericML, this verdict is produced by a machine learning system.
Trojan-Downloader.AndroidOS.Necro.d (1.56%), designed for downloading and running other malware on infected devices, climbed to sixteenth place from seventeenth.
Trojan-SMS.AndroidOS.Agent.ado dropped from fifteenth to seventeenth place with 1.54%. This malware sends text messages to short codes.
Trojan-Dropper.AndroidOS.Hqwar.gen, which unpacks and runs various banking Trojans on a device, kept eighteenth place with 1.54%.
Trojan-Downloader.AndroidOS.Agent.kx (1.45%), which loads adware, dropped to the bottom of the rankings.
Geography of mobile threats
https://e.infogram.com/_/5488dBZS93CY789cAis8?parent_url=https%3A%2F%2Fsecurelist.com%2Fit-threat-evolution-in-q2-2022-mobile-statistics%2F107123%2F&src=embed#async_embed
Map of attempts to infect mobiles with malware, Q2 2022 (download)
TOP 10 countries and territories by share of users attacked by mobile malware
| Countries and territories* | %** | |
| 1 | Iran | 26,91 |
| 2 | Yemen | 17,97 |
| 3 | Saudi Arabia | 12,63 |
| 4 | Oman | 12,01 |
| 5 | Algeria | 11,49 |
| 6 | Egypt | 10,48 |
| 7 | Morocco | 7,88 |
| 8 | Kenya | 7,58 |
| 9 | Ecuador | 7,19 |
| 10 | Indonesia | 6,91 |
* Excluded from the rankings are countries and territories with relatively few (under 10,000) Kaspersky mobile security users.
** Unique users attacked as a percentage of all users of Kaspersky mobile security solutions in the country.
Iran remained the leader in terms of the share of infected devices in Q2 2022 with 26.91%; the most widespread threats there as before were the annoying AdWare.AndroidOS.Notifyer and AdWare.AndroidOS.Fyben families. Yemen rose to second place with 17.97%; the Trojan-Spy.AndroidOS.Agent.aas spyware was the threat most often encountered by users in that country. Saudi Arabia came third with 12.63%, the most common malware apps in the country being the AdWare.AndroidOS.Adlo and AdWare.AndroidOS.Fyben adware families.
Mobile banking Trojans
The number of detected mobile banking Trojan installation packages increased slightly compared to the previous quarter: during the reporting period, we found 55,614 of these, an increase of 1,667 on Q1 2022 and a year-on-year increase of 31,010.
Almost half (49.28%) of the detected installation packages belonged to the Trojan-Banker.AndroidOS.Bray family. The Trojan-Banker.AndroidOS.Wroba was second with 5.54%, and Trojan-Banker.AndroidOS.Fakecalls third with 4.83%.
https://e.infogram.com/_/WmVkKmoCinRxAPQXWFha?parent_url=https%3A%2F%2Fsecurelist.com%2Fit-threat-evolution-in-q2-2022-mobile-statistics%2F107123%2F&src=embed#async_embed
Number of installation packages for mobile banking Trojans detected by Kaspersky, Q2 2021 — Q2 2022 (download)
Ten most common mobile bankers
| Verdict | %* | |
| 1 | Trojan-Banker.AndroidOS.Bian.h | 23.22 |
| 2 | Trojan-Banker.AndroidOS.Anubis.t | 10.48 |
| 3 | Trojan-Banker.AndroidOS.Svpeng.q | 7.88 |
| 4 | Trojan-Banker.AndroidOS.Asacub.ce | 4.48 |
| 5 | Trojan-Banker.AndroidOS.Sova.g | 4.32 |
| 6 | Trojan-Banker.AndroidOS.Gustuff.d | 4.04 |
| 7 | Trojan-Banker.AndroidOS.Ermak.a | 4.00 |
| 8 | Trojan-Banker.AndroidOS.Agent.ep | 3.66 |
| 9 | Trojan-Banker.AndroidOS.Agent.eq | 3.58 |
| 10 | Trojan-Banker.AndroidOS.Faketoken.z | 2.51 |
* Unique users attacked by this malware as a percentage of all Kaspersky mobile security solution users who encountered banking threats.
https://e.infogram.com/_/bawulAIMCMSwfujrqAJT?parent_url=https%3A%2F%2Fsecurelist.com%2Fit-threat-evolution-in-q2-2022-mobile-statistics%2F107123%2F&src=embed#async_embed
Geography of mobile banking threats, Q2 2022 (download)
TOP 10 countries and territories by shares of users attacked by mobile banking Trojans
| Countries and territories* | %** | |
| 1 | Spain | 1.04 |
| 2 | Turkey | 0.71 |
| 3 | Australia | 0.67 |
| 4 | Saudi Arabia | 0.64 |
| 5 | Switzerland | 0.38 |
| 6 | UAE | 0.23 |
| 7 | Japan | 0.14 |
| 8 | Colombia | 0.14 |
| 9 | Italy | 0.10 |
| 10 | Portugal | 0.09 |
* Countries and territories with relatively few users of Kaspersky mobile security solutions (under 10,000) have been excluded from the ranking.
** Unique users attacked by mobile banking Trojans as a percentage of all Kaspersky mobile security solution users in the country.
In Q2 2022, Spain still had the largest share of unique users attacked by mobile financial threats: 1.04%. Trojan-Banker.AndroidOS.Bian.h accounted for 89.95% of attacks on Spanish users. Turkey had the second-largest share (0.71%), with attacks on Turkish users dominated by Trojan-Banker.AndroidOS.Ermak.a (41.38%). Australia was third with 0.67%; most attacks in this country were attributed to Trojan-Banker.AndroidOS.Gustuff.d (96,55%).
Mobile ransomware Trojans
The number of mobile ransomware Trojan installation packages we detected in Q2 2022 (3,821) almost doubled from Q1 2022, increasing by 1,879; the figure represented a year-on-year increase of 198.
https://e.infogram.com/_/qgwrjBbIOWRSVBiw4z6r?parent_url=https%3A%2F%2Fsecurelist.com%2Fit-threat-evolution-in-q2-2022-mobile-statistics%2F107123%2F&src=embed#async_embed
Number of installation packages for mobile ransomware Trojans detected by Kaspersky, Q2 2021 — Q2 2022 (download)
Top 10 most common mobile ransomware
| Verdict | %* | |
| 1 | Trojan-Ransom.AndroidOS.Pigetrl.a | 76.81 |
| 2 | Trojan-Ransom.AndroidOS.Rkor.ch | 2.66 |
| 3 | Trojan-Ransom.AndroidOS.Small.as | 2.51 |
| 4 | Trojan-Ransom.AndroidOS.Rkor.br | 1.46 |
| 5 | Trojan-Ransom.AndroidOS.Rkor.bi | 1.40 |
| 6 | Trojan-Ransom.AndroidOS.Svpeng.ah | 1.29 |
| 7 | Trojan-Ransom.AndroidOS.Congur.cw | 1.23 |
| 8 | Trojan-Ransom.AndroidOS.Small.cj | 1.14 |
| 9 | Trojan-Ransom.AndroidOS.Svpeng.ac | 1.14 |
| 10 | Trojan-Ransom.AndroidOS.Congur.bf | 1.07 |
* Unique users attacked by the malware as a percentage of all Kaspersky mobile security solution users attacked by ransomware Trojans.
https://e.infogram.com/_/fLxtf6iaN8E9XJOQQUsF?parent_url=https%3A%2F%2Fsecurelist.com%2Fit-threat-evolution-in-q2-2022-mobile-statistics%2F107123%2F&src=embed#async_embed
Geography of mobile ransomware Trojans, Q2 2022 (download)
TOP 10 countries and territories by share of users attacked by mobile ransomware Trojans
| Countries and territories* | %** | |
| 1 | Yemen | 0,30 |
| 2 | Kazakhstan | 0,19 |
| 3 | Azerbaijan | 0,06 |
| 4 | Kyrgyzstan | 0,04 |
| 5 | Switzerland | 0,04 |
| 6 | Egypt | 0,03 |
| 7 | Saudi Arabia | 0,03 |
| 8 | Uzbekistan | 0,02 |
| 9 | Russian Federation | 0,02 |
| 10 | Morocco | 0,02 |
* Excluded from the rankings are countries and territories with relatively few (under 10,000) Kaspersky mobile security users.
** Unique users attacked by ransomware Trojans as a percentage of all Kaspersky mobile security solution users in the country or territory.
Countries leading by number of users attacked by mobile ransomware Trojans were Yemen (0.30%), Kazakhstan (0.19%) and Azerbaijan (0.06%). Users in Yemen most often encountered Trojan-Ransom.AndroidOS.Pigetrl.a, while users in Kazakhstan and Azerbaijan were attacked mainly by members of the Trojan-Ransom.AndroidOS.Rkor family.
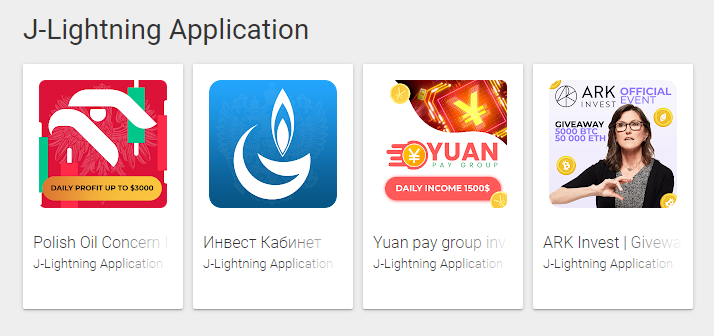

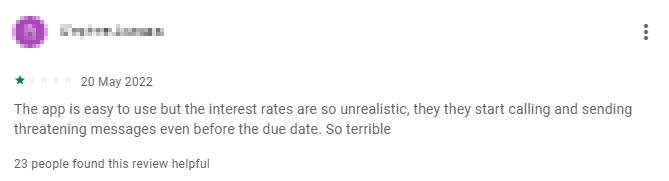

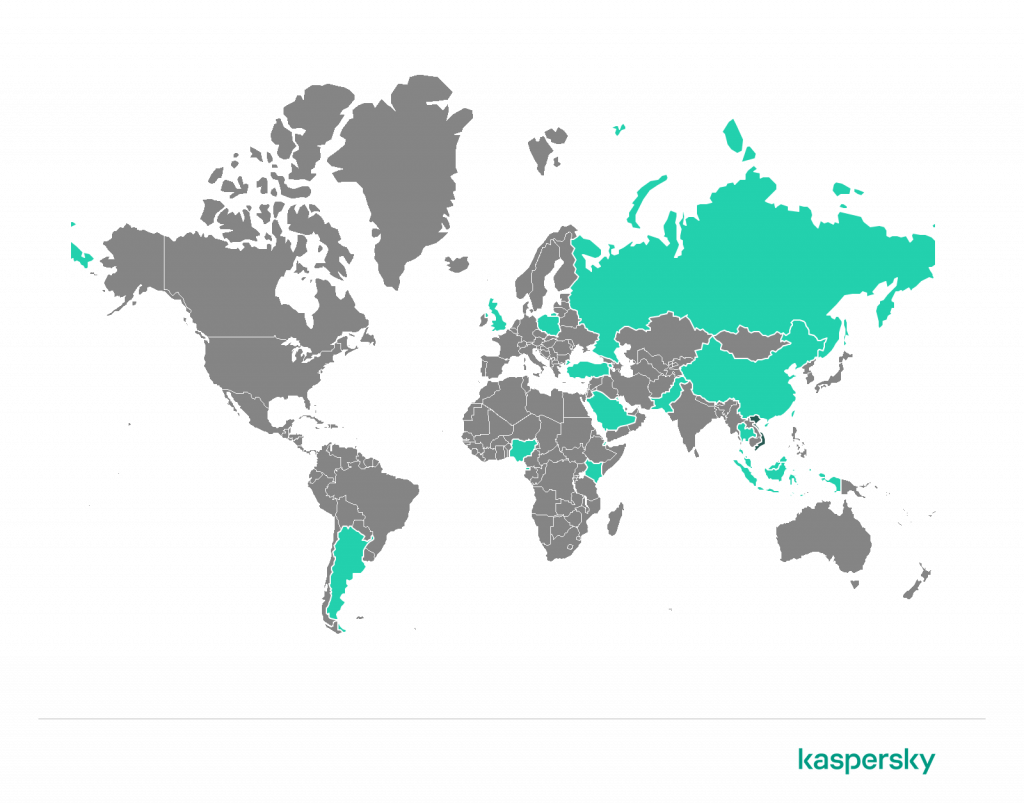
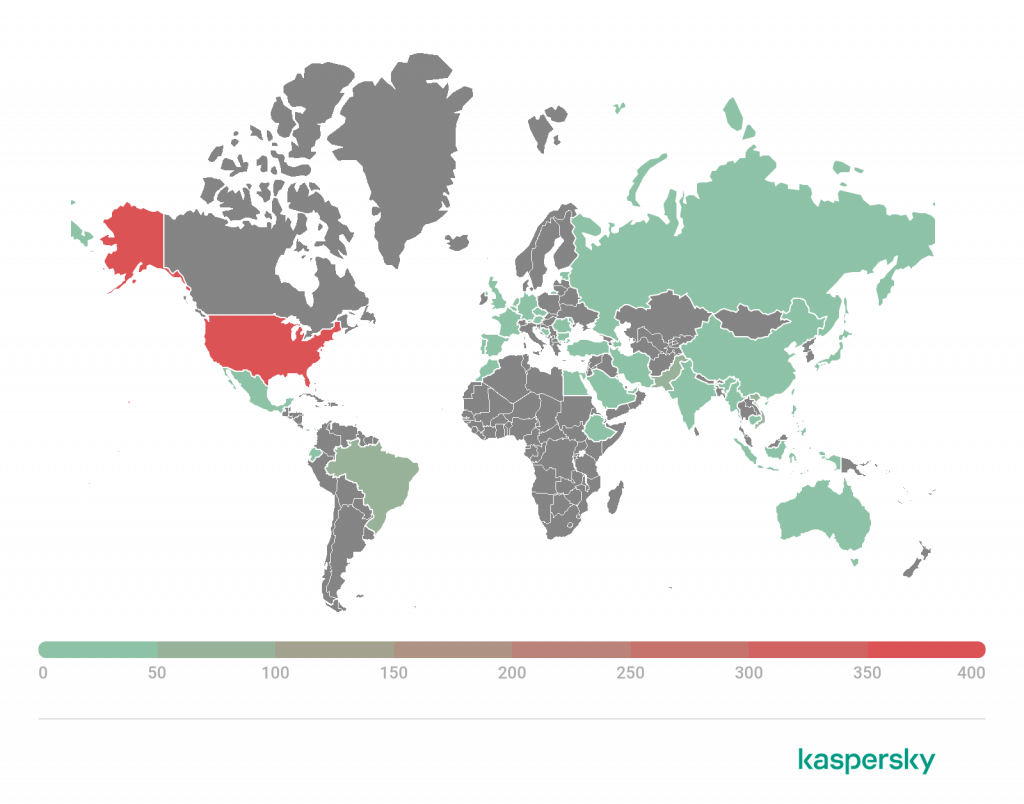
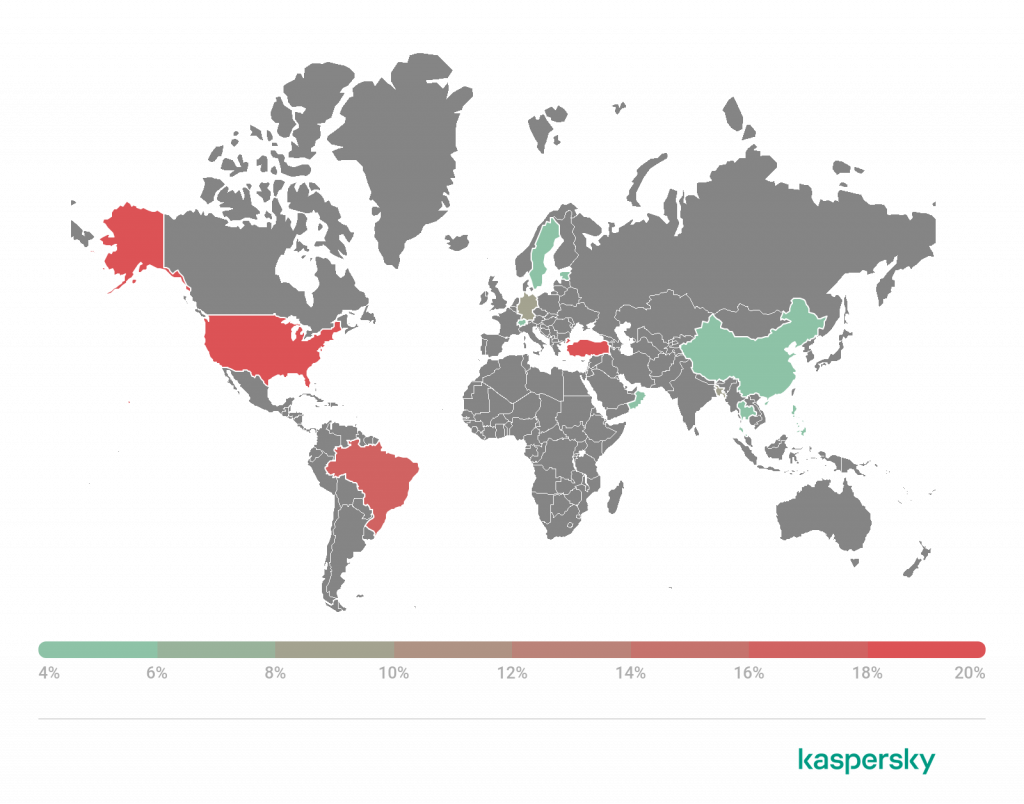
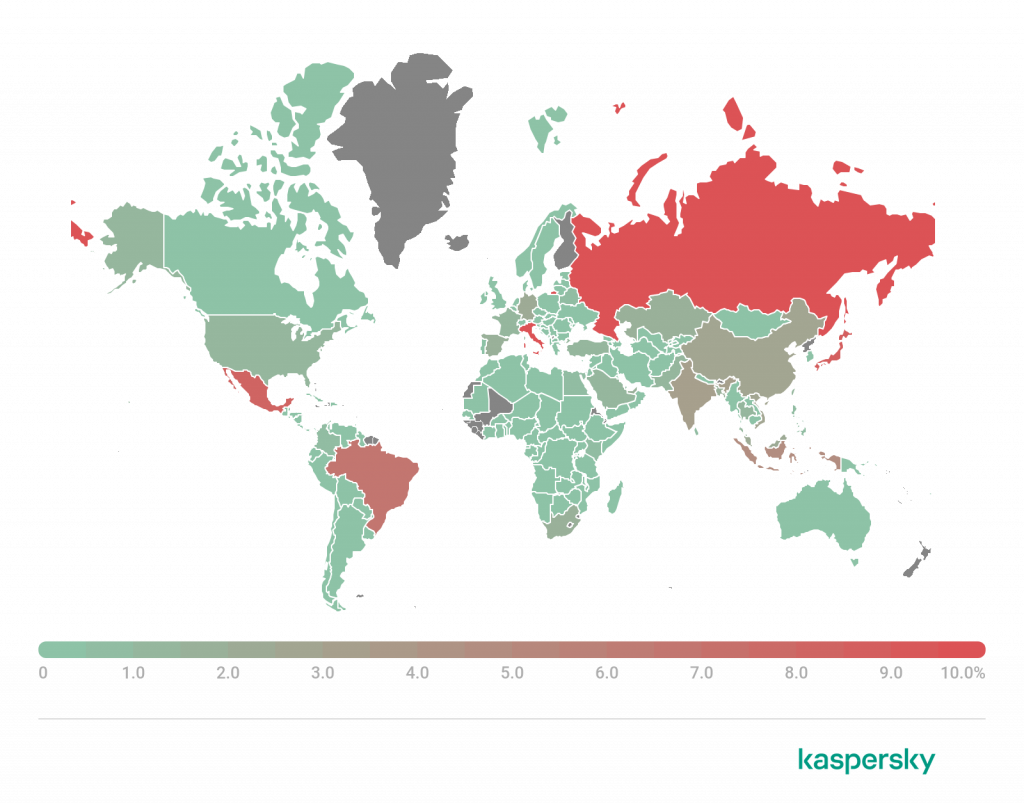
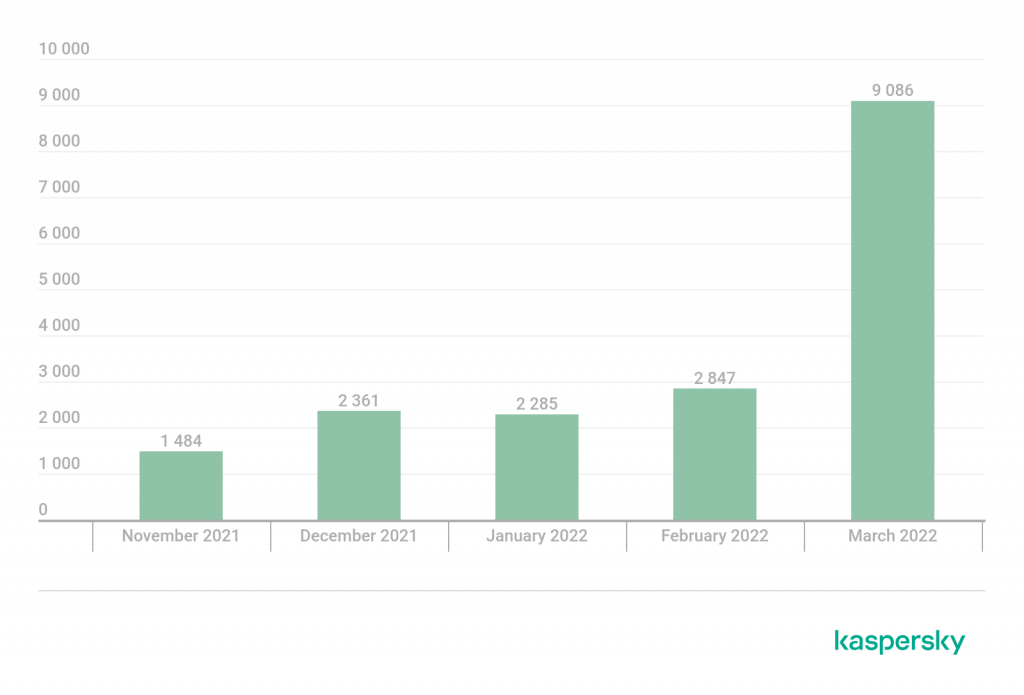
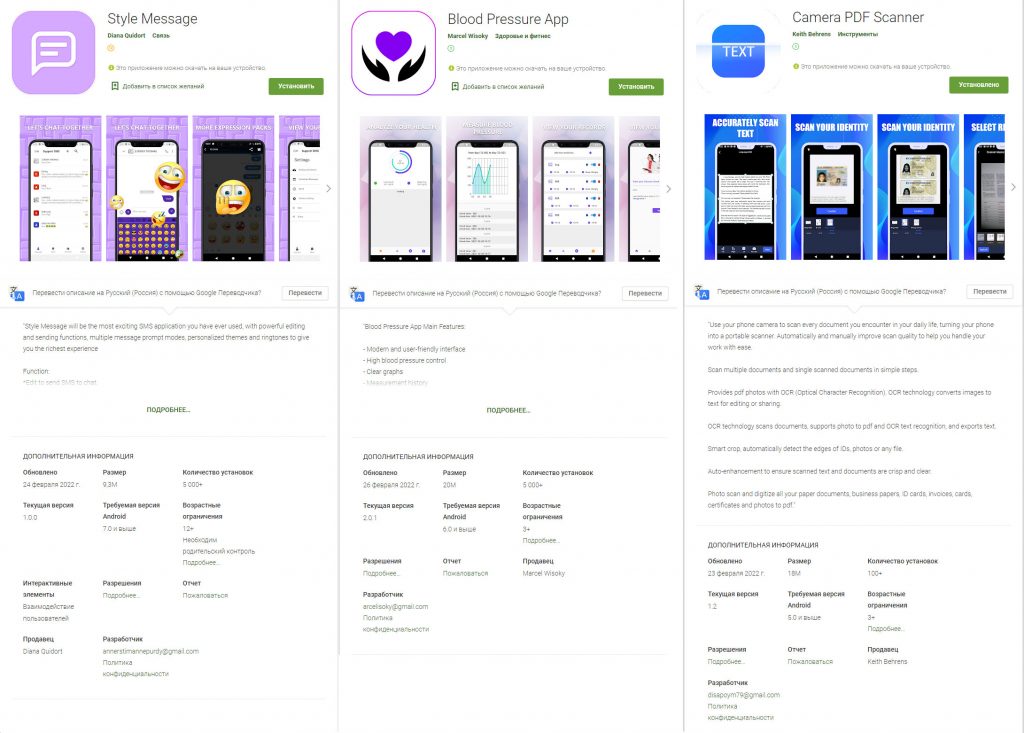
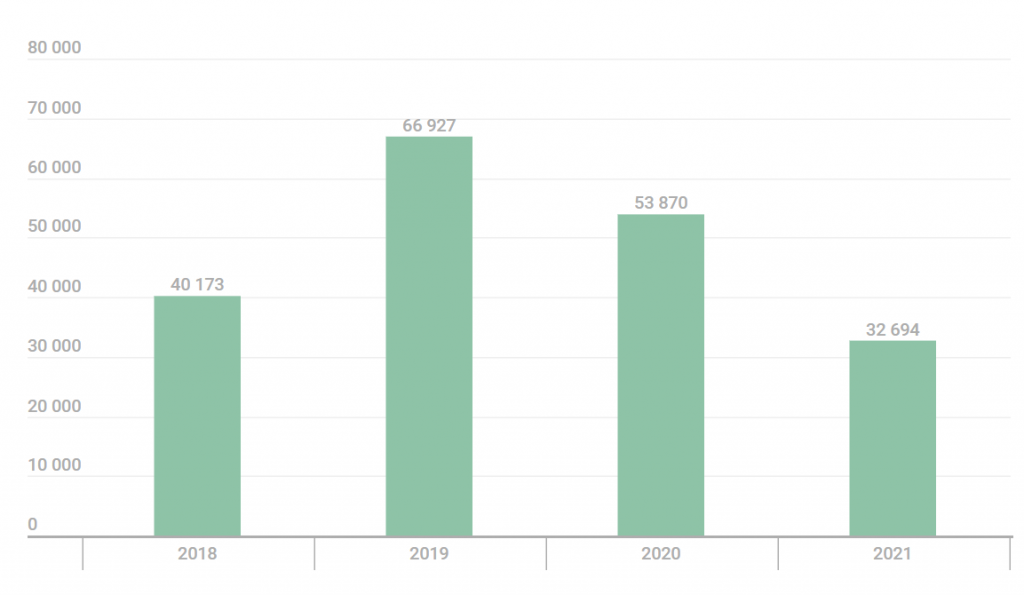
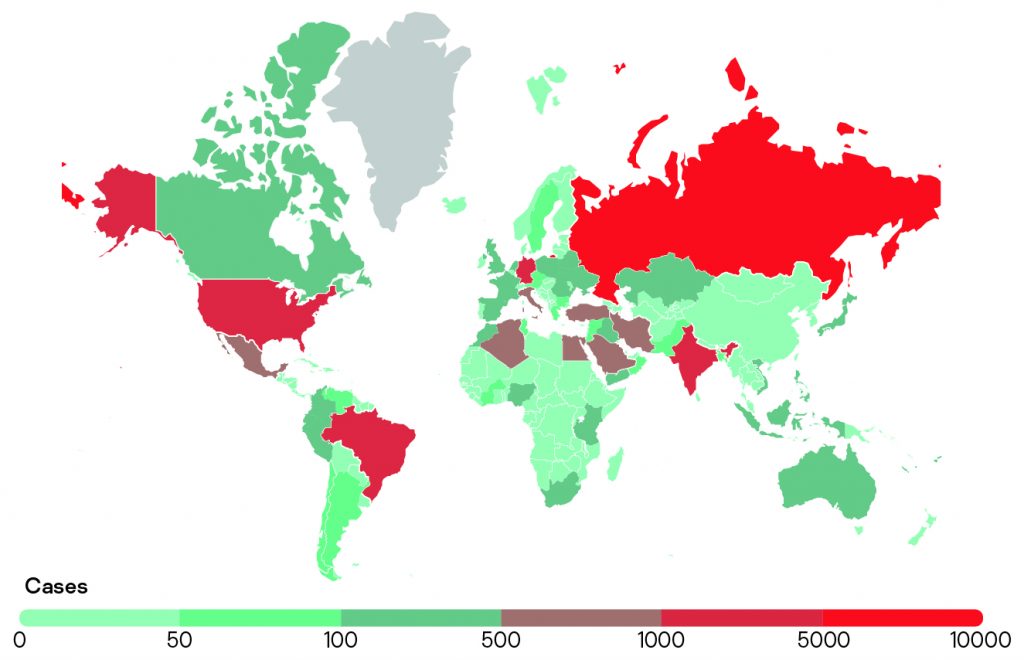






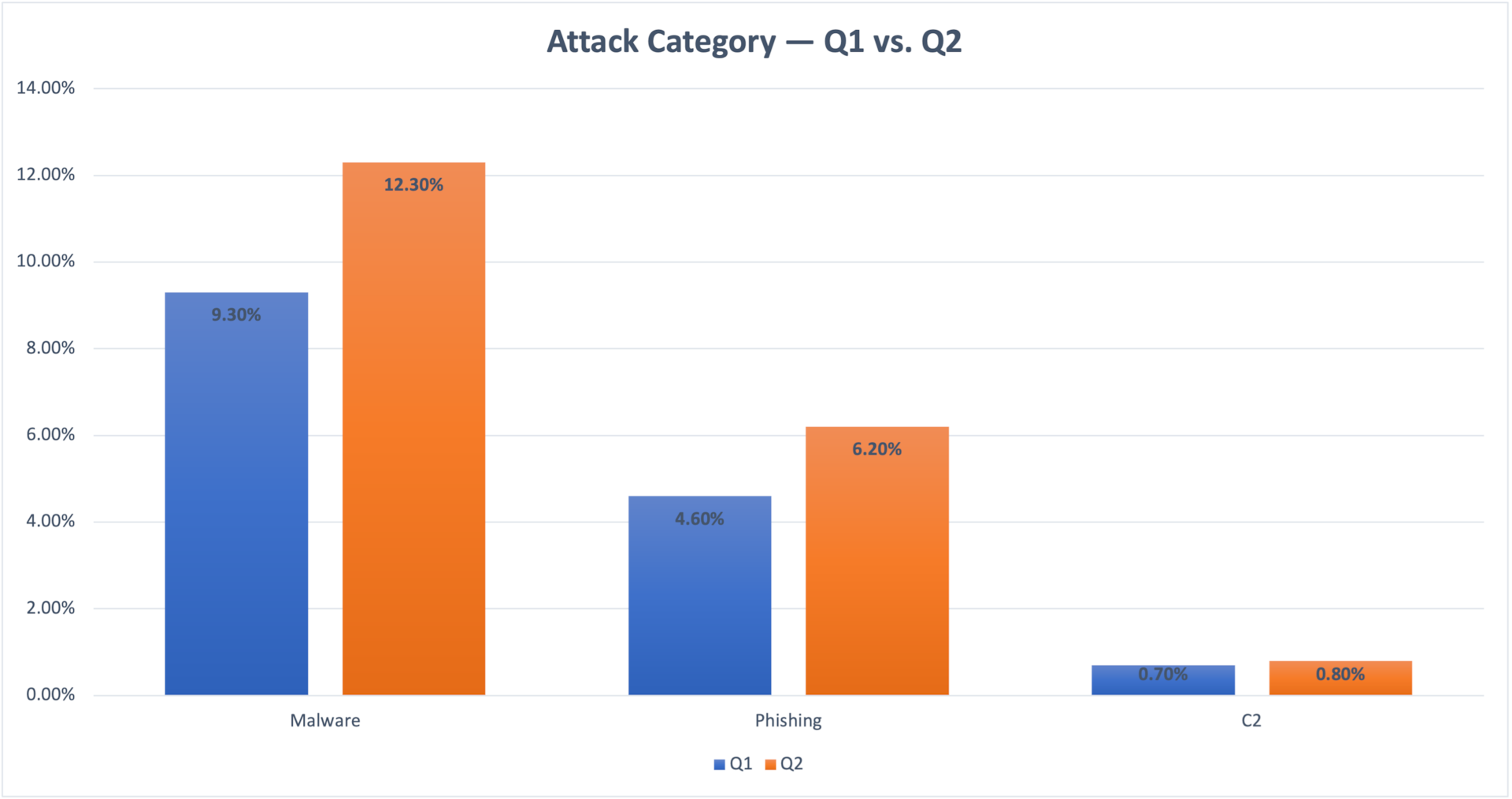 Fig. 1: Devices exposed to threats — Q1 vs. Q2
Fig. 1: Devices exposed to threats — Q1 vs. Q2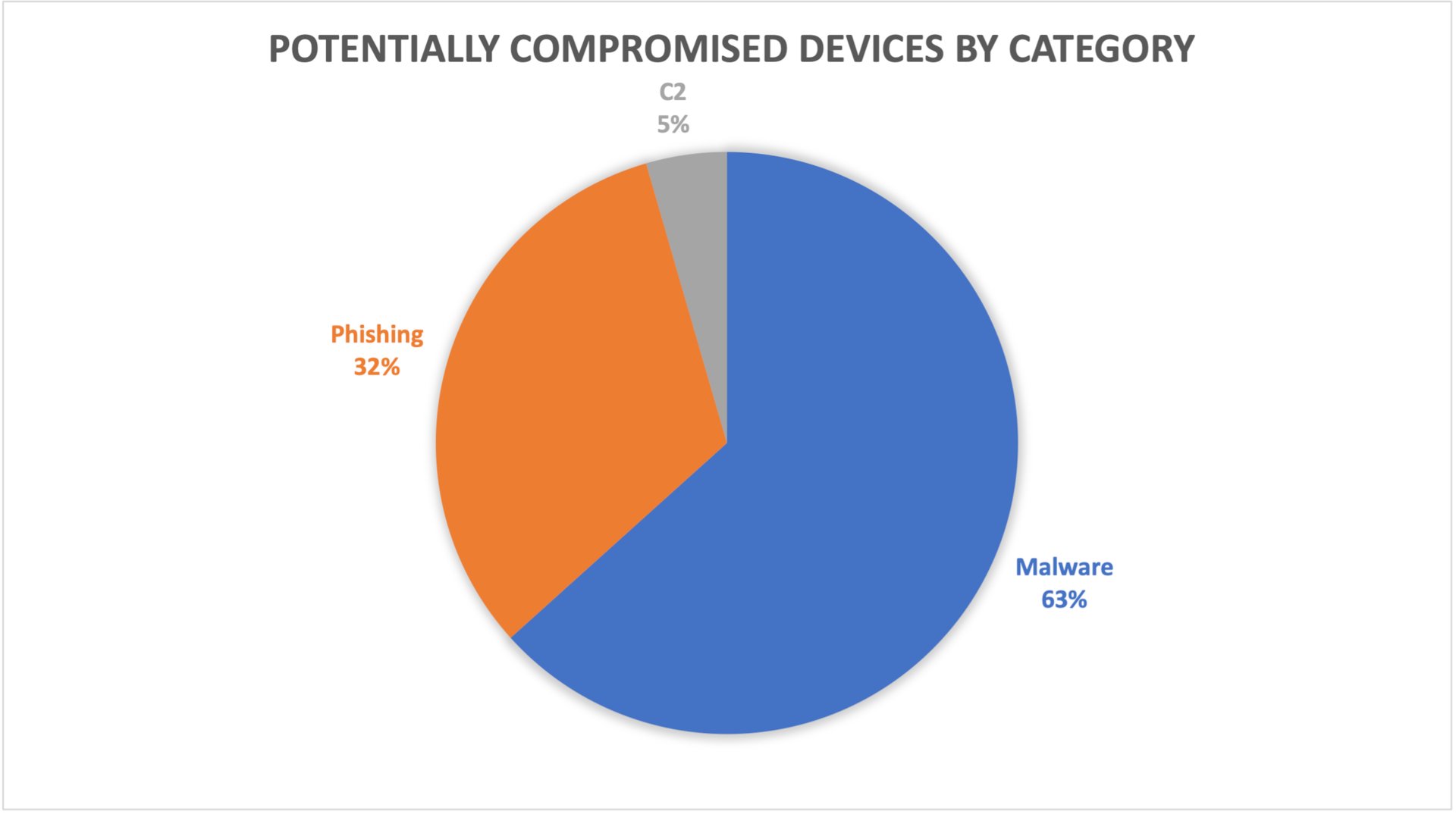 Fig. 2: Potentially compromised devices by category
Fig. 2: Potentially compromised devices by category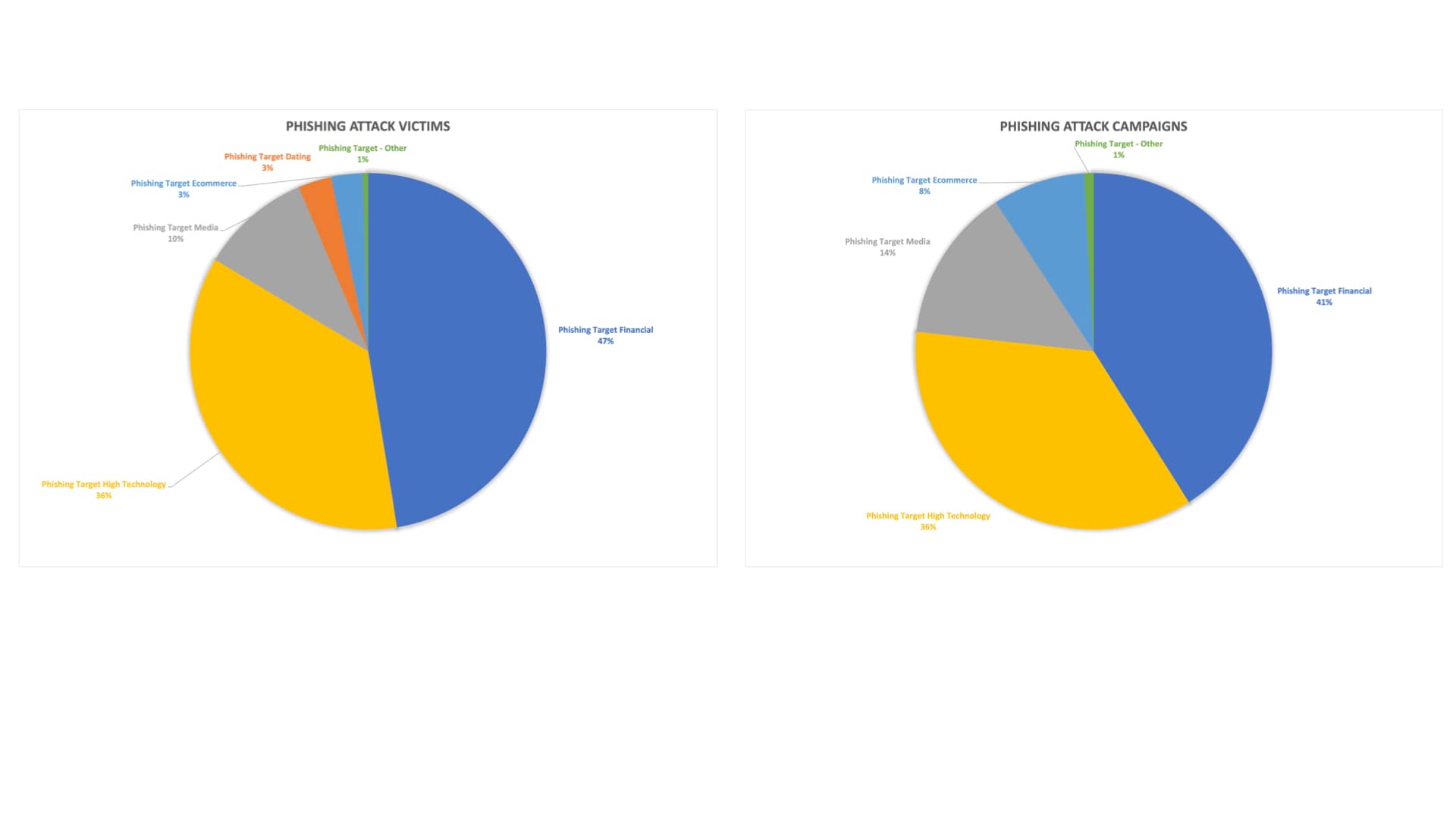 Fig. 3: Phishing victims and phishing campaigns by abused brands
Fig. 3: Phishing victims and phishing campaigns by abused brands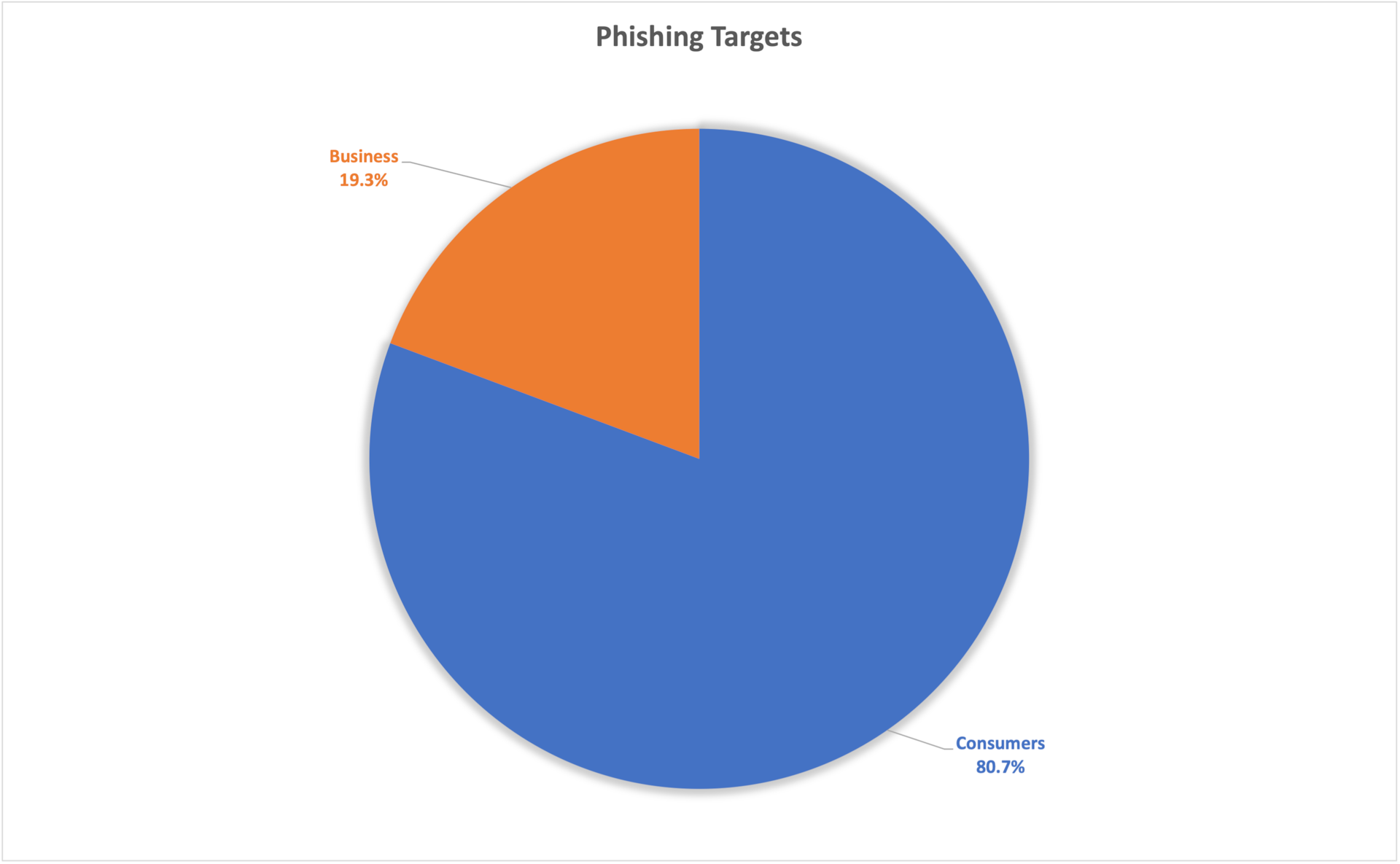 Fig. 4: Phishing targeted accounts — consumers vs. business
Fig. 4: Phishing targeted accounts — consumers vs. business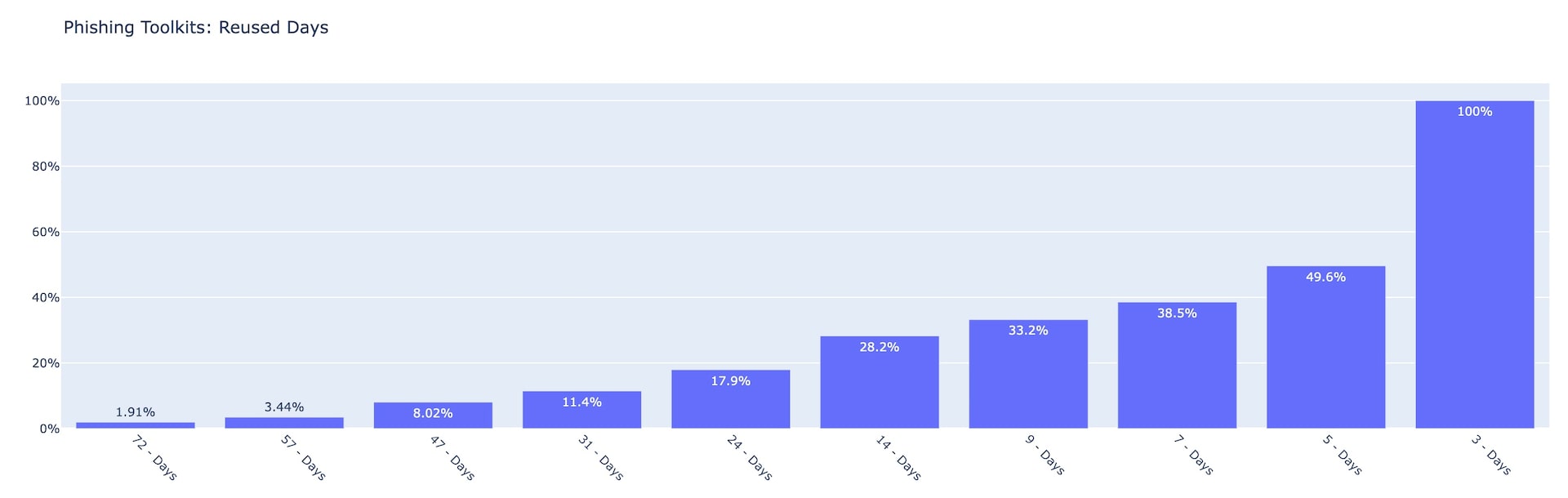 Fig. 5: Phishing toolkits by number of reused days Q2 2022
Fig. 5: Phishing toolkits by number of reused days Q2 2022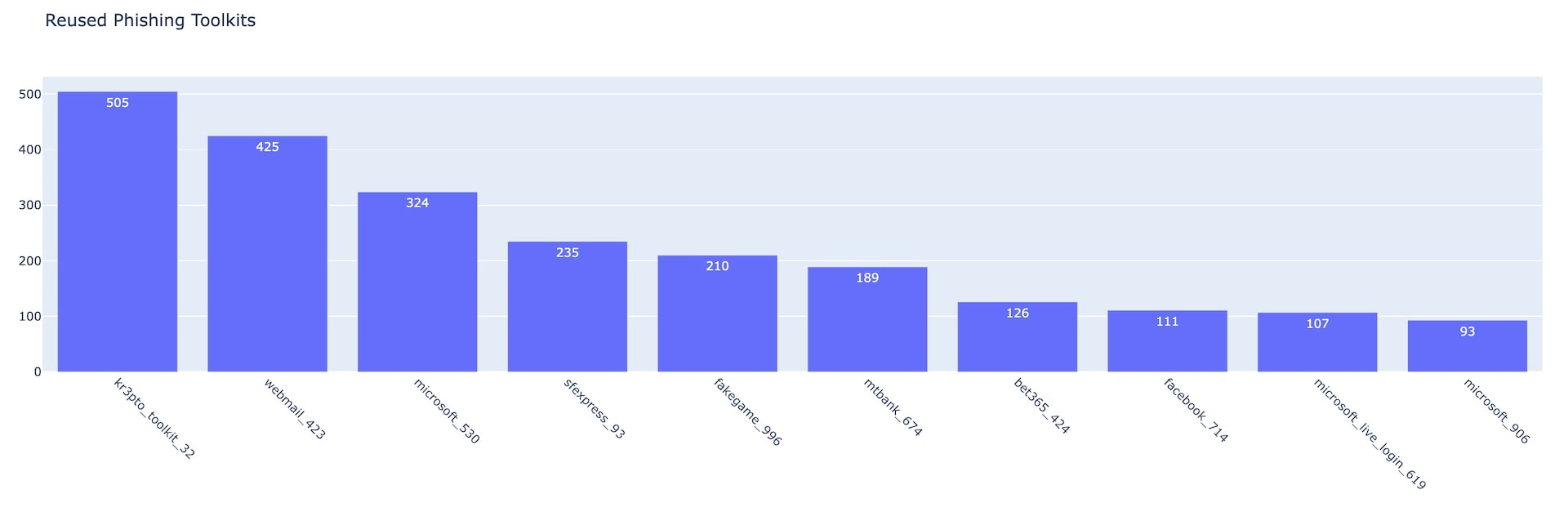 Fig. 6: Top 10 reused phishing toolkits
Fig. 6: Top 10 reused phishing toolkits